A worldwide attack erupted on June 27 with a high concentration of hits in Ukraine – including the Ukrainian central bank, government offices and private companies.
The attack is distributing what seems to be a variant of Petya, an MBR ransomware. While the source of the attack has yet to be determined, many researchers suggest that M.E.Doc, a Ukrainian accounting software provider, was compromised and its systems abused to distribute the attack via its software update mechanism. M.E.Doc is a popular service in Ukraine, the malware’s top targeted country; in May the company was also suspected of involvement in the distribution of another ransomware, known as XData.
So far, M.E.Doc has denied the accusations and posted on Facebook that while their network was infected and encrypted as part of the attack, their software updates are still intact. As of now, our attempts to contact M.E.Doc directly have failed.
Once the malware infiltrates into a network, it makes lateral movement in order to infect the entire network. The malware’s lateral movement is likely due to having worm-capabilities such as: exploiting SMB vulnerabilities, abusing active sessions, stolen credentials and file-shares as means to deliver the file from one machine to another.
In particular, we were able to see an attempt to spread in the victim’s network by leveraging the EternalBlue exploit, used previously in WannaCry, an exploit for CVE-2017-0147 as well as another executable embedded as a resource in the malware’s binary that serves as a credential stealer. The latter is a DLL, dropped in the %TEMP% directory and executed with rundll. The tool itself resembles a known open source utility called Mimikatz, which has abilities to steal hashes, passwords and other security related artifacts from a machine’s memory.
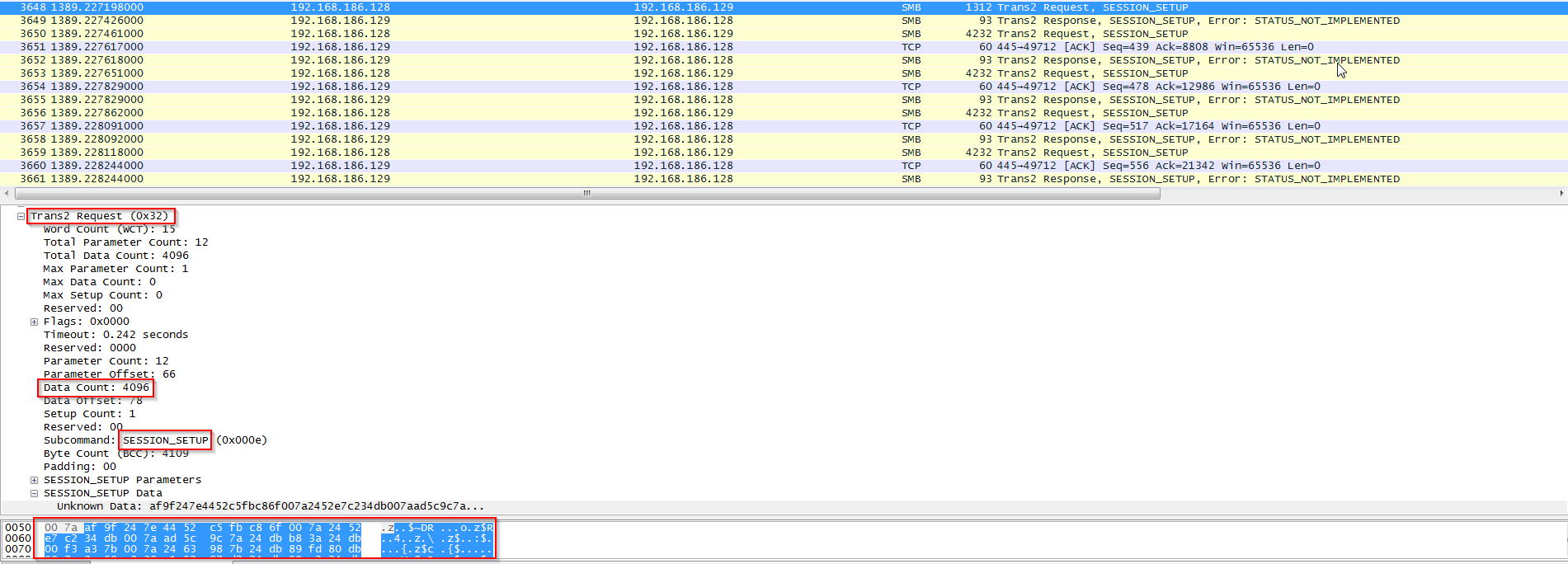
The stolen credentials are later used in order to attempt a file delivery of the Petya dll to the target host. The Petya payload can be seen transferred via TRANS2 SESSION_SETUP request packets of the SMB protocol, sent as 4096k chunks (one chunk per request). It is encoded with the XOR key: 24db007a. When the file is obtained by the victim machine, it is being run remotely with a legitimate Sysinternals tool called PsExec (also embedded in the original malware binary).
Figure 1: an example of a Petya payload chunk’s transfer
The malware used in the attack has a hard-coded BitCoin wallet, meaning that all victims of this sample are directed to pay ransom into the same wallet. Currently (June 28, 14:00 CET), the wallet only contains 3.874 BitCoins, which is under $10,000.
Check Point is closely following the attack, and investigating Petya’s lateral movement, as well as the potential involvement of Loki-Bot info-stealer in the campaign. We keep adding protections to our Threat Prevention solutions, and encourage all customers to update to the latest online package.
The below solutions protect against Petya ransomware and Loki Bot:
- SandBlast: https://www.checkpoint.com/products/sandblast-network-security/
- SandBlast Agent: https://www.checkpoint.com/products/endpoint-sandblast-agent/
- Anti-Bot: https://www.checkpoint.com/products/anti-bot-software-blade/
- IPS: https://www.checkpoint.com/products/ips-software-blade/
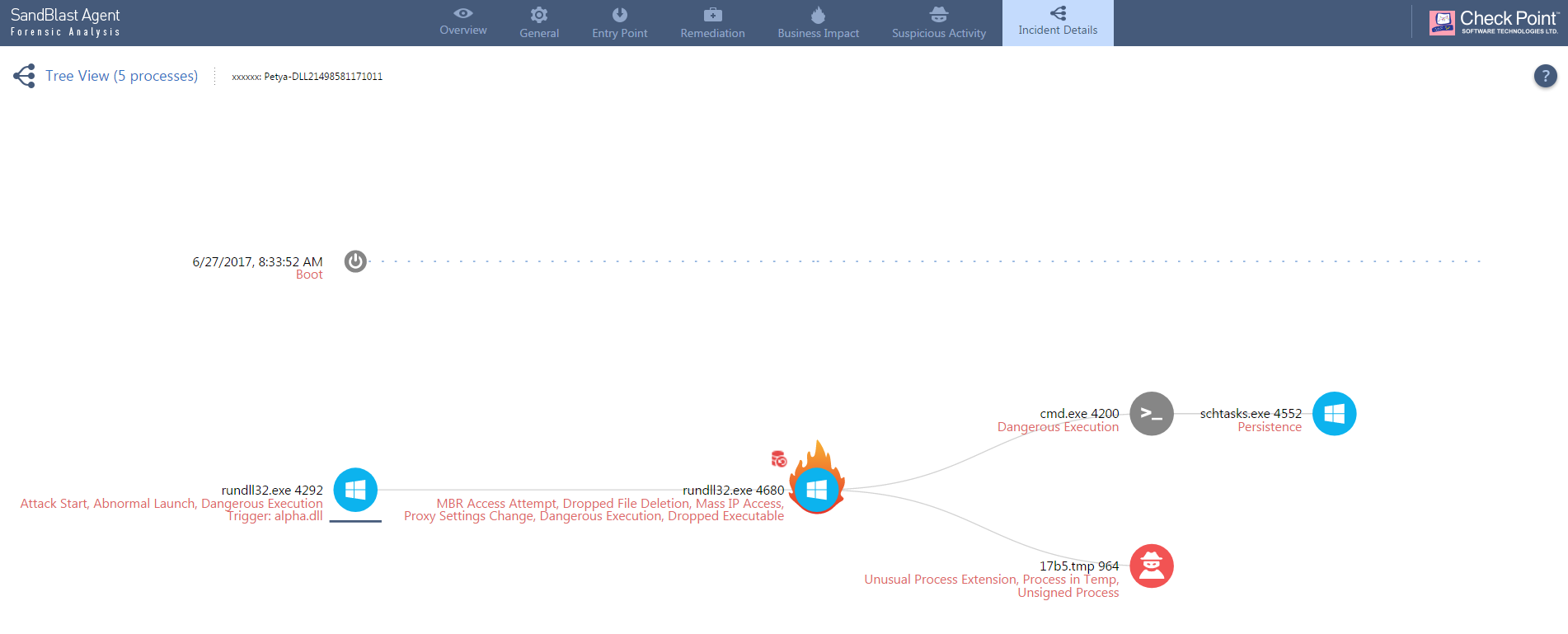
Demo: Petya Stopped and Analyzed by Check Point Anti Ransomware
Click here to see our forensic analysis