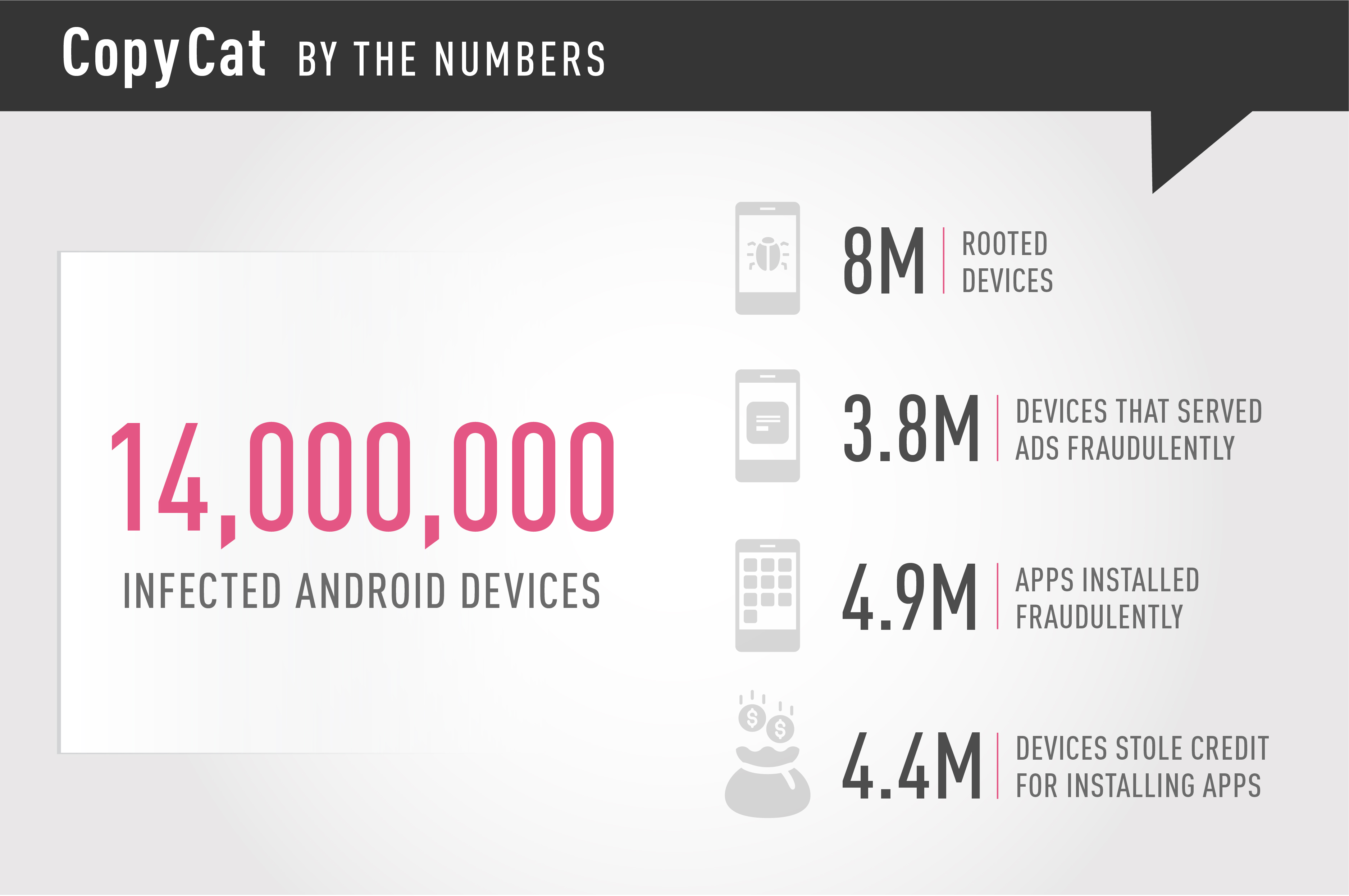
Check Point researchers identified a mobile malware that infected 14 million Android devices, rooting approximately 8 million of them, and earning the hackers behind the campaign approximately $1.5 million in fake ad revenues in two months.
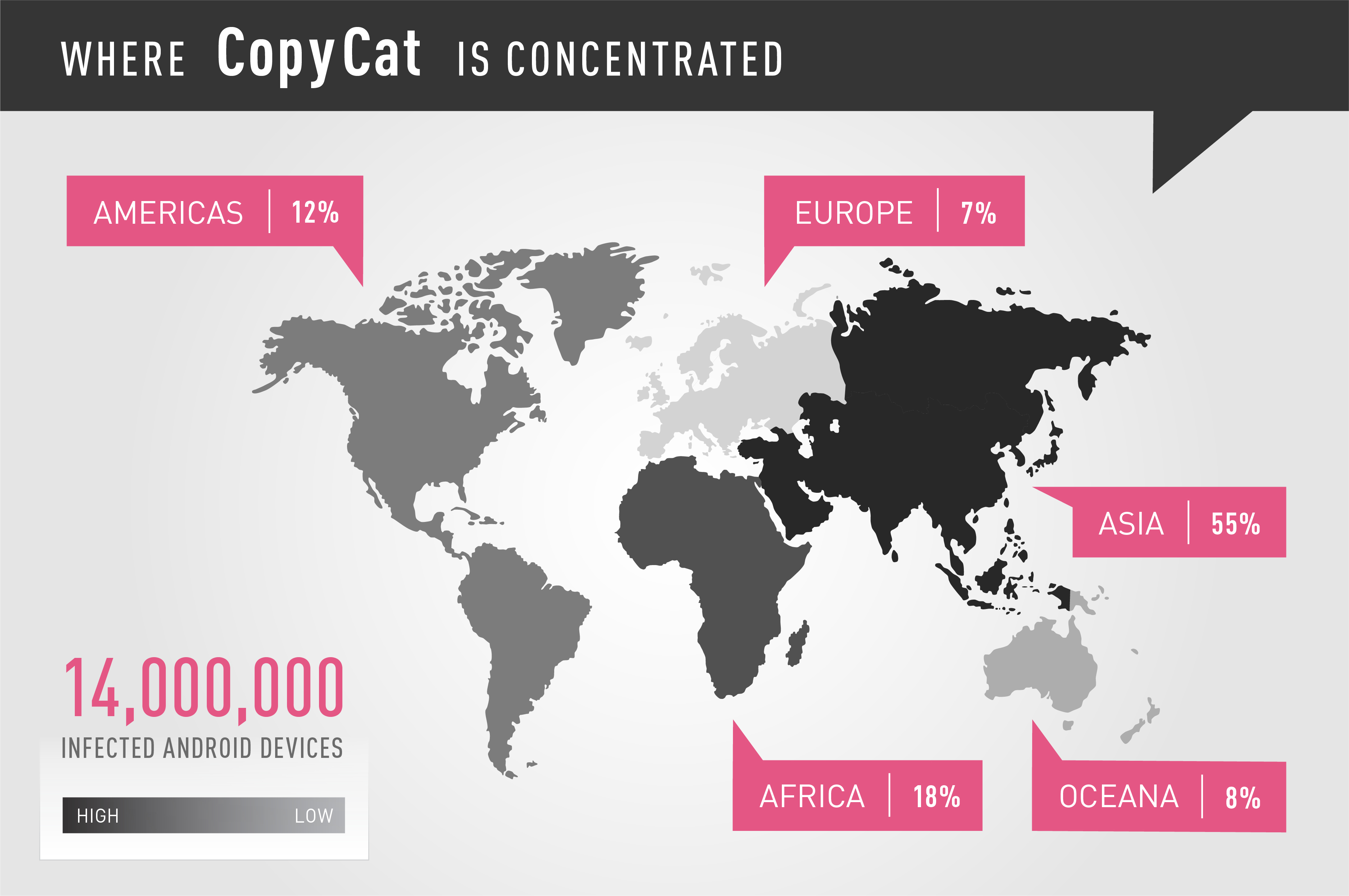
The malware, dubbed CopyCat by Check Point mobile threat researchers, uses a novel technique to generate and steal ad revenues. While CopyCat infected users mainly in Southeast Asia, it spread to more than 280,000 Android users in the United States.
CopyCat is a fully developed malware with vast capabilities, including rooting devices, establishing persistency, and injecting code into Zygote – a daemon responsible for launching apps in the Android operating system – that allows the malware to control any activity on the device.
Researchers first encountered the malware when it attacked devices at a business protected by Check Point SandBlast Mobile. Check Point retrieved information from the malware’s Command and Control servers, and conducted a full reverse engineering of its inner workings, which are detailed in a comprehensive technical report.
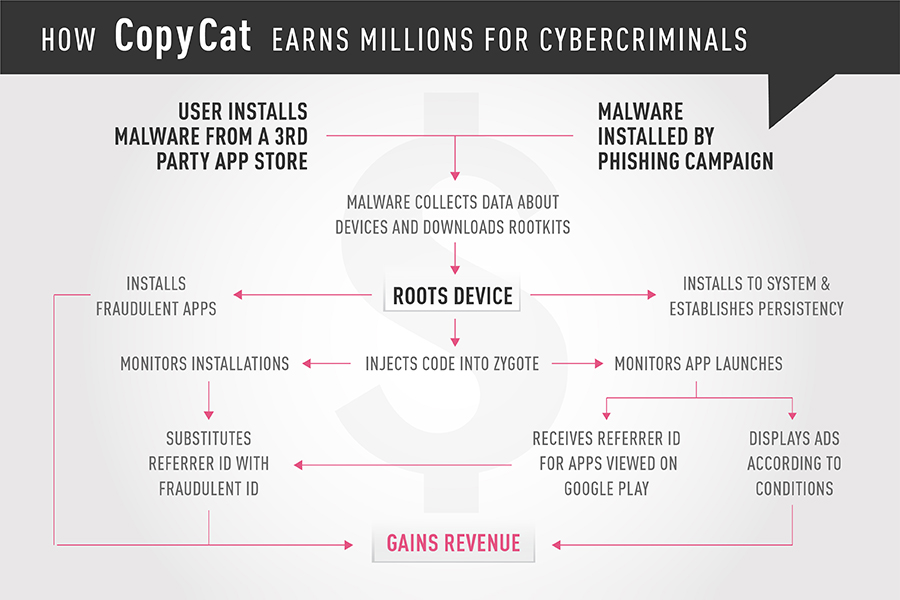
 The CopyCat campaign reached its peak between April and May 2016. Researchers believe the campaign spread via popular apps, repackaged with the malware and downloaded from third party app stores, as well as phishing scams. There was no evidence that CopyCat was distributed on Google Play, Google’s official app store.
The CopyCat campaign reached its peak between April and May 2016. Researchers believe the campaign spread via popular apps, repackaged with the malware and downloaded from third party app stores, as well as phishing scams. There was no evidence that CopyCat was distributed on Google Play, Google’s official app store.
In March 2017, Check Point informed Google about the CopyCat campaign and how the malware operated. According to Google, they were able to quell the campaign, and the current number of infected devices is far lower than it was at the time of the campaign’s peak. Unfortunately, devices infected by CopyCat may still be affected by the malware even today.
What does CopyCat do?
CopyCat is an extensive campaign that infected 14 million devices globally, rooting 8 million of them, in what researchers describe as an unprecedented success rate. Check Point researchers estimate that the malware generated $1.5 million for the group behind the campaign.
Read the CopyCat research report
CopyCat uses state-of-the-art technology to conduct various forms of ad fraud, similar to previous malware discovered by Check Point, such as Gooligan, DressCode, and Skinner. Upon infection, CopyCat first roots the user’s device, allowing the attackers to gain full control of the device, and essentially leaving the user defenseless.
CopyCat then injects code into the Zygote app launching process, allowing the attackers to receive revenues by getting credit for fraudulently installing apps by substituting the real referrer’s ID with their own. In addition, CopyCat abuses the Zygote process to display fraudulent ads while hiding their origin, making it difficult for users to understand what’s causing the ads to pop-up on their screens. CopyCat also installs fraudulent apps directly to the device, using a separate module. These activities generate large amounts of profits for the creators of CopyCat, given the large number of devices infected by the malware.
What’s the big deal about adware?
The preponderance of malware focused on skimming profit from the ad industry, and the ingenious technical approaches deployed, indicate just how lucrative it is for cybercriminals to engage in adware campaigns. But adware poses a significant threat to users and businesses, alike, including:
- Theft of sensitive information – Some adware, such as Gooligan, steal sensitive information from their victims, which can later be sold to third parties
- Device rooting or jailbreaking – Adware frequently roots or jailbreaks devices, thereby breaking the built-in security mechanisms of Android or iOS, leaving victims defenseless to even the lowest level kind of hacks
- Evolving attack objectives – The bad guys behind adware campaigns may refocus their attacks, spreading different types of malware to rooted or jailbroken devices, or use them to create Denial of Service attacks
- Code sharing with hacking community – The sophisticated capabilities developed by adware developers can be adopted by other malware developers, and used to commit bigger crimes, as witnessed in the Vault 7 leak.
Adware impacts businesses, too
For these reasons, adware such as CopyCat create risk to both private users and to the enterprise. Attackers need nothing more than a compromised mobile device connected to the corporate network to breach the business’ complete network and gain access to sensitive data. Mobile devices are an endpoint in your network, just like any laptop, and require the same level of protection. Adware that steals credentials to sensitive information, or roots devices and leaves them vulnerable to any type of attack, are exactly what an attacker looking to infiltrate a corporate network seeks.
Who is behind CopyCat?
Surprisingly, several adware families were developed by firms connected to the ad industry. Such was the case with HummingBad and YiSpecter, developed by Yingmob, and the recent example of the Judy malware, developed by Kiniwini. It is unclear who is behind the CopyCat attack, however, there are several connections to MobiSummer, an ad network located in China. It is important to note that while these connections exist, it does not necessarily mean the malware was created by the company, and it is possible the perpetrators behind it used MobiSummer’s code and infrastructure without the firm’s knowledge.
The first connection between the company and the malware is the server, which operates both the malware and some of MobiSummer’s activity. In addition, some of the malware’s code is signed by MobiSummer itself, and some of the remote services used by the malware were created by the company. The malware also refrains from targeting Chinese devices, suggesting the malware developers are Chinese and want to avoid any investigation by local law enforcement, a common tactic in the malware world.
What’s the impact?
Check Point researchers investigated one of the Command and Control servers, which was active between April and May 2016, and recorded over 14 million infected devices, 8 million of them rooted (54%). Fraudulent ads were display on 3.8 million of the infected devices (26%), while 4.4 million, or 30%, of the infected devices were used to steal credit for installing apps on Google Play. The Command and Control server also stored information collected about the infected devices, including brand, model, OS version, and country. Check Point researchers believe additional Command and Control servers operating CopyCat exist, indicating that the number of infected devices may be significantly larger.
Protect your enterprise | Protect your personal device
The revenue generated by the attackers is estimated to be more than $1.5 million, most of which was earned over the course of two months. The nearly 100 million ads displayed by the malware generated approximately $120,000. Since we can measure only how many devices claimed credit for fraudulent installations, and not how many times such an activity took place, we are conservatively assuming that each device has done so only once. Even so, the estimated revenue these actions yielded for the perpetrators is over $660,000. The largest revenue stream came from the 4.9 million fraudulent app installations conducted by the CopyCat, generating over $735,000.
How does the malware operate?
Once installed, the malware lies in waiting until the device is restarted, so that a connection isn’t made between the installation of the app and the malicious activity. Once the device has restarted, CopyCat downloads an “upgrade” pack from an S3 bucket, a web storage service provided by Amazon. This pack contains six common exploits with which the malware attempts to root the device. If successful, CopyCat installs another component to the device’s system directory, an activity which requires root permissions, and establishes persistency, making it difficult to remove.
CopyCat then injects code into the Zygote process, from which all Android apps are launched. Since all apps in Android are processes launched from Zygote, injecting code directly into it allows the malware to infiltrate the activity of all running apps. This is the first adware discovered using this technique, which was first introduced by the financial malware Triada.
After CopyCat compromises the Zygote process, it injects into the system_server process, and contains all Android services, such as PhoneManager, Packagemanager, etc., including ActivityManager. CopyCat then registers for several events on the system server. The malware uses two tactics to steal ad revenue – displaying fraudulent ads and stealing referrer IDs of apps installed from Google Play.
Displaying fraudulent ads
To display fraudulent ads, the malware uses “callActivityOnStart” and “callActivityOnStop,” which are executed each time a device activity launches. When an activity starts, the malware checks three things: whether the user is in China; whether the launched app is one of the predefined list of major apps, such as Facebook and WhatsApp (to avoid interfering with them); and whether enough time has passed since the last ad was displayed. If none of these conditions are met, the malware displays an ad from the ad libraries of Facebook, Admob, or UC. These predefined conditions are meant to minimize the user’s suspicion, while disguising the app that’s the source of the pop-up ads.
Stealing app installation credits
The second tactic is even more complex, but carries more profits for the perpetrators. Advertisers are paid for displaying ads that lead to the installation of certain apps.
Read the CopyCat research report
CopyCat hooks into the “startActivityLockedStub” in the system_server process, and monitors it to detect the launching of the Google Play process. Once launching the process, CopyCat retrieves the package name of the app that the user is viewing on Google Play, and sends it to its Command and Control server. The server sends back a referrer ID suited for the package name. This referrer ID belongs to the creators of the malware, and will later be used to make sure the revenue for the installation is credited to them.
CopyCat blocks all install_referrer intents and replaces them with its own referrer ID, which was received from the Command and Control server previously.
Installing fraudulent apps
CopyCat also operates a separate module that conducts fraudulent app installations based on its root permissions. This module operates on a very low level of the Android operating system, taking advantage of Android’s package manager. The package manager monitors specific directories: /system/app and /data/app.
When an APK file appears in one of these directories, the package manager installs it. The malware makes use of this process, and copies the APK files of the fraudulent apps it wants to install to the /data/app directory, from which the package manager will install it. The malware verifies whether the app was installed, and reports the result to the Command and Control server.
 How could CopyCat root so many devices?
How could CopyCat root so many devices?
CopyCat successfully rooted over 54% of the devices it infected, which is very unusual even with sophisticated malware. CopyCat uses several exploits as part of its operation: CVE-2014-4321, CVE-2014-4324, CVE-2013-6282 (VROOT), CVE-2015-3636 (PingPongRoot), and CVE-2014-3153 (Towelroot). All of these exploits, relevant for Android versions 5 and earlier, are both widely used and very old, with the most recent discovered more than two years ago. Even though patches for these exploits were released, CopyCat successfully used them to root eight million devices. These old exploits are still effective because users patch their devices infrequently, or not at all. Following the QuadRooter vulnerabilities, we learned that 64% of Android users have old security patches, leaving them exposed to attack strategies that have already been patched.
How to stay protected
Cutting-edge malware such as CopyCat requires advanced protections, capable of identifying and blocking zero-day malware by using both static and dynamic app analysis. Only by examining the malware within context of its operation on a device can successful strategies to block it be created. Users and enterprises should treat their mobile devices just like any other part of their network, and protect them with the best cybersecurity solutions available.
Check Point customers are protected by SandBlast Mobile, and on the network front by Check Point Anti-Bot blade, which provides protection against this threat with the signature: Trojan.AndroidOS.CopyCat.