Research By: Feixiang He, Bohdan Melnykov, Elena Root
Key Findings:
- RottenSys, a mobile adware, has infected nearly 5 million devices since 2016.
- Indications show the malware could have entered earlier in the supplier chain.
- The attackers have been testing a new botnet campaign via the same C&C server.
The Check Point Mobile Security Team has discovered a new widespread malware family targeting nearly 5 million users for fraudulent ad-revenues. They have named it ‘RottenSys’ for in the sample we encountered it was initially disguised as a System Wi-Fi service.
How Does the Malware Operate?
Spotting the Malware:
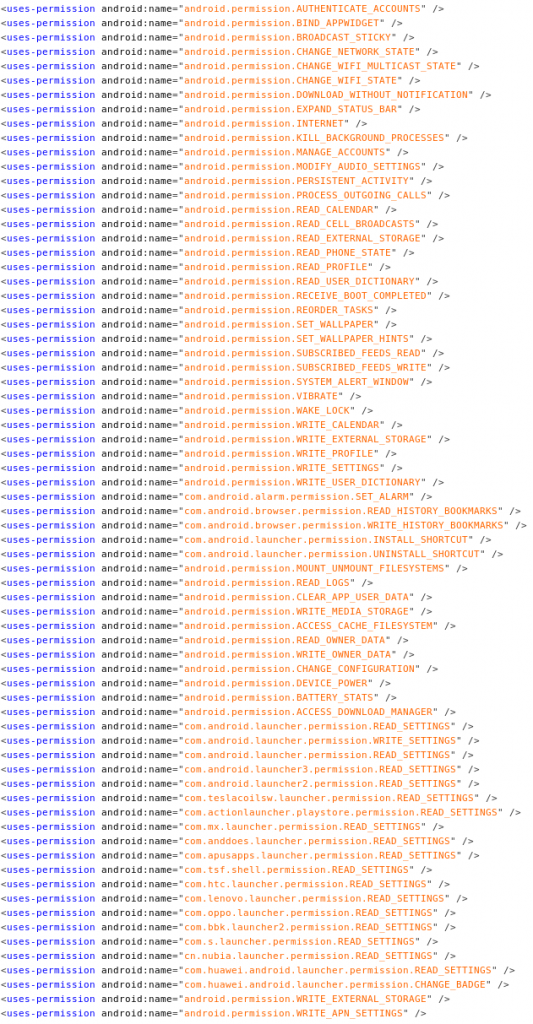
Recently, an unusual self-proclaimed system Wi-Fi service (系统WIFI服务) on a Xiaomi Redmi phone caught our eyes. Our engines show this application does not provide any secure Wi-Fi related service to users. Instead, it asks for many sensitive Android permissions such as accessibility service permission, user calendar read access and silent download permission, which are not related to Wi-Fi service.
Figure 1: List of permissions requested by the app
RottenSys’s Malicious Operation
RottenSys uses two evasion techniques. The first is postponing its operation for a set time, to avoid connection between the malicious app and the malicious activity.
As its second evasive tactic, RottenSys contains only a dropper component, which does not display any malicious activity at first. Once the device is active and the dropper is installed, it contacts its Command and Control (C&C) server which sends it a list of additional components required for its activity. These components contain the actual malicious code and are downloaded from the C&C server after the dropper receives the list.
RottenSys downloads these components silently, using the DOWNLOAD_WITHOUT_NOTIFICATION permission which does not require any user interaction. Usually, the malware downloads three additional components.
After all necessary components are downloaded, RottenSys uses an open-sourced Android framework called ‘Small’ (github.com/wequick/small), which is an Android application virtualization framework. This framework allows all components to run alongside each other at the same time and achieve the combined malicious functionality of an extensive rough ad network, displaying advertisements on the device’s home screen, as pop-up windows or as full screen ads.
RottenSys is adapted to use the Guang Dian Tong (Tencent ads platform) and Baidu ad exchange for its ad fraud operation.
Figure 2: Code snippets of the small framwork combining functionalities
To avoid having its operation shut down by the Android system, RottenSys uses another open source framework called MarsDaemon (github.com/Marswin/MarsDaemon). While MarsDaemon keeps processes alive, it also hinders the device’s performance and drains the battery. Users in Chinese Android forums have noticed and complained about both side effects of the app, as well as aggressive advertisements:
Figure 3: User reports aggressive home screen advertisement on Xiaomi forum
Figure 4: User reported device’s poor performance
following activity of a Rottensys varient.
There are numerous other similar user complaints. The earliest mentions directly connected to RottenSys apps can be dated back to October 2017.
A Tailored Operation
According to our findings RottenSys has a big fleet of variants of the payloads mentioned earlier (the dropper and the additional components). Each variant is tailored for different campaign, device type, advertisement platform, and spread channel.
| Typical payload name | Function | Number of variants we observed |
| com.zdfbqmt.app.main | The actual entry point of the malicious features | 89 |
| com.jtwmy.lib.gdt | Responsible for rough advertisement activities | 54 |
| Zip file contains
com.jtwmy.lib.gdt com.zdfbqmt.lib.ui |
Responsible for status monitoring, reporting, scheduling.
These also represent the different sub rough adnetwork campaigns |
173 |
In the list of observed malware distribution channels, we saw two names (“天湃浅装” and “天湃桌面”) which suggest a possible connection to a Hangzhou based mobile phone supply chain distributor Tian Pai.
Tian Pai related channels contribute 49.2% of the total number of infested devices that we observed. According to China National Enterprise Credit Information Publicity System, Tian Pai offers a wide range of services from presales customization, online/offline wholesale to customer care. It covers regional sales of top brands in the market such as Samsung, HTC, Apple, Xiaomi, ZTE, Coolpad, Lenovo, and Huawei.
Tian Pai may not be a direct participant in the campaign. Yet, this correlates with our hypothesis that the malware entered the user’s device before purchase.
What Is the Effect?
We managed to go even further in researching this threat and obtain data which shows the real extent of this malicious campaign.
We identified two parallel C&C servers which were used by RottenSys for its operation. We also managed to analyze the attacks and define separate channels in which the attackers operate and even ascertain the volume of infected devices and fraudulent ads displayed to users.
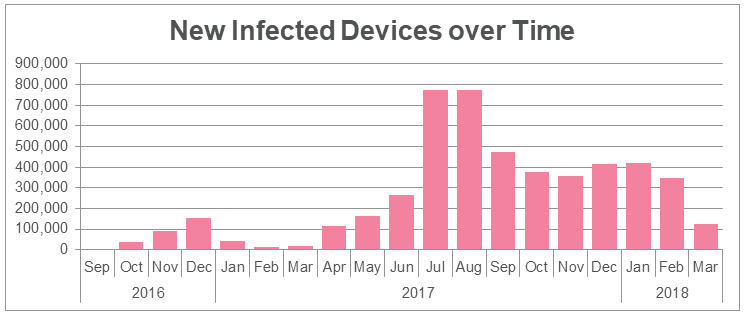
Measuring the Impact
According to our findings, the RottenSys malware began propagating in September 2016. By March 12, 2018, 4,964,460 devices were infected by RottenSys. The top impacted mobile devices brands are Honor, Huawei, and Xiaomi.
As our hunting progressed, we uncovered several more C&C servers used in different variants of RottenSys initial droppers. Hence, we believe the real number of victims could be much larger.
It’s All About the Money
RottenSys is an extremely aggressive ad network. In the past 10 days alone, it popped aggressive ads 13,250,756 times (called impressions in the ad industry), and 548,822 of which were translated into ad clicks. As an example for the possible revenue stream attackers enjoy from this malware, we calculated the revenue from these impressions and clicks according to the conservative estimation of 20 cents for each click and 40 cents for each thousand impressions. According to these calculations, the attackers earned over $115k from their malicious operation in the last ten days alone!
| Date | Clicks | Impressions | Income (USD) |
| 2018/03/12 | 50182 | 1207662 | 10,519.46 |
| 2018/03/11 | 52859 | 1352329 | 11,112.73 |
| 2018/03/10 | 53019 | 1315820 | 11,130.13 |
| 2018/03/09 | 52136 | 1293821 | 10,944.73 |
| 2018/03/08 | 56496 | 1306264 | 11,821.71 |
| 2018/03/07 | 57529 | 1326055 | 12,036.22 |
| 2018/03/06 | 56418 | 1321140 | 11,812.06 |
| 2018/03/05 | 55688 | 1342616 | 11,674.65 |
| 2018/03/04 | 58209 | 1395028 | 12,199.81 |
| 2018/03/03 | 56286 | 1390021 | 11,813.21 |
| Total | 548822 | 13250756 | $115,064.7 |
Exploring New Fields of Operations
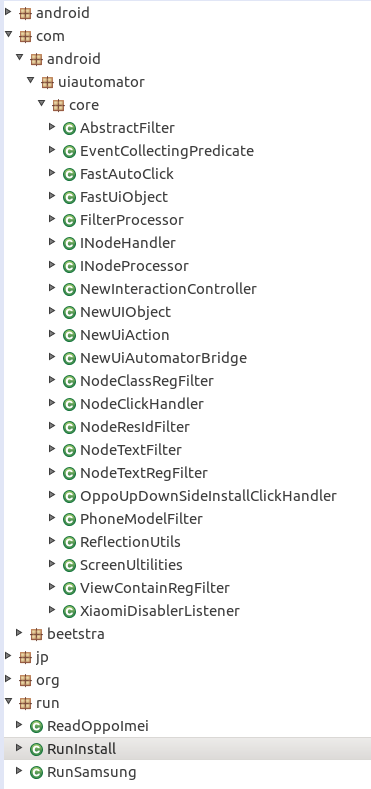
While investigating RottenSys we discovered evidence that the attackers are up to something far more damaging than simply displaying uninvited advertisements. Apparently, the attackers have been testing a new botnet campaign via the same C&C server since the beginning of February 2018.
The attackers plan to leverage Tencent’s Tinker application virtualization framework as a dropper mechanism. The payload which will be distributed can turn the victim device into a slave in a larger botnet. This botnet will have extensive capabilities including silently installing additional apps and UI automation. Interestingly, a part of the controlling mechanism of the botnet is implemented in Lua scripts. Without intervention, the attackers could re-use their existing malware distribution channel and soon grasp control over millions of devices.
Figure 5: Botnet malicious payload Jar file
Mitigation
Locating the source of rough aggressive advertisement displayed on Android home screen is always challenging for common users. Mitigating is even harder. Luckily, Users can uninstall the RottenSys dropper if they know the exact package name to remove. If your brand new phone is suffering from unknown ads on the home screen, please go to Android system settings, then to app manager, and look for the following possible malware package names and uninstall them:
| Package Name | App Name |
| com.android.yellowcalendarz | 每日黄历 |
| com.changmi.launcher | 畅米桌面 |
| com.android.services.securewifi | 系统WIFI服务 |
| com.system.service.zdsgt |
Final Thoughts
In just a few hours, it will be World Consumer Rights Day 2018. This is not the first time we’ve seen mobile devices compromised even before they reach common consumers. Only two weeks ago, Dr. Web reported similar case where malware are embedded in some cheap models of Android phone firmware.
Although the impacted brands and malware mechanism are largely different this time, the problem is very real. Who should safeguard Android devices before they are purchased by end users? How to make sure common users enjoy untampered and safe new mobile devices? There’s no quick answer. Industry must act, for digital safety is a key consumer right.
We are open to share additional technical details with law enforcement agencies and facilitate further mitigation of consumer risks.