

Introduction
Recently, Check Point engines detected a new phishing campaign impersonating the Royal Bank of Canada (RBC).
The attack starts by sending legitimate-looking e-mails containing a PDF attachment to multiple organizations and victims from Canada:

Figure 1: Phishing e-mail
Looking into the detected artifacts revealed an ongoing phishing attack that has been going after customers of Canadian banks for at least two years. By sending highly convincing e-mails to their targets, constantly registering look-alike domains for popular banking services in Canada and crafting tailor-made documents, the attackers behind this were able to run a large-scale operation and remain under the radar for a long time.
Phishing Flow
The PDF attachment uses the Royal Bank’s logo, as well as an authorization code that the victim supposedly needs to renew their digital certificate for the RBC express online banking systems:

Figure 2: PDF attachment
When the victim clicks on any of the URLs which appear in the above document, they are led to a phishing page asking them to enter their RBC express credentials.
Although the phishing website looks identical to the login page in the official RBC website, the attackers did not invest a lot of effort into replicating it. They simply took a screenshot of the official website, and added invisible textboxes on top of the input fields to harvest the victim’s credentials:

Figure 3: Phishing page
After the victim tries to sign in, they are taken to a registration page where they are asked to enter the authorization code received via the phishing e-mail:

Figure 4: Victim is asked to insert the authorization code
Lastly, the victim is asked to wait while a digital certificate is supposedly being registered for them:

Figure 5: Victim’s registration is being processed
Old Documents
There were multiple variants of the PDF attachments, with slight differences between them. However, some of the textual instructions they contained were repetitive, used unique phrasing and appeared in more than one document.
This allowed us to hunt for more samples and find related PDFs dating back to 2017:


To evade detection, the PDFs were password-protected in some cases, and the password was mentioned in the e-mail’s body:

Figure 7: Password-protected attachments
Connecting the Dots
The phishing website which appeared in the PDF attachments we investigated at first (royalexpressprofile[.]com) resolved to a Ukrainian IP address: 176.119.1[.]80.
Examining this IP address revealed that it hosted more domains impersonating RBC in addition to other banks:
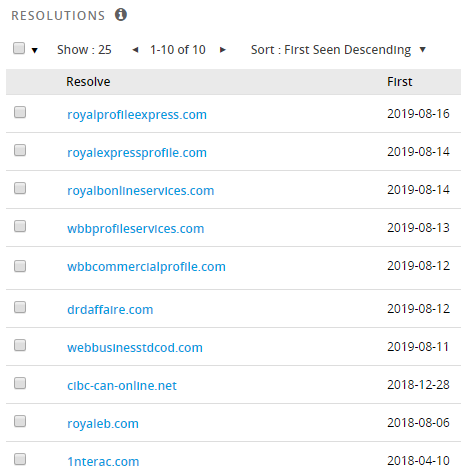
Figure 8: Domains resolving to 176.119.1[.]80
As it turns out, there were many more IP addresses on the same netblock 176.119.1[.]0/24 that were part of a massive infrastructure used to launch phishing attacks that attempt to steal banking credentials from Canadian victims:
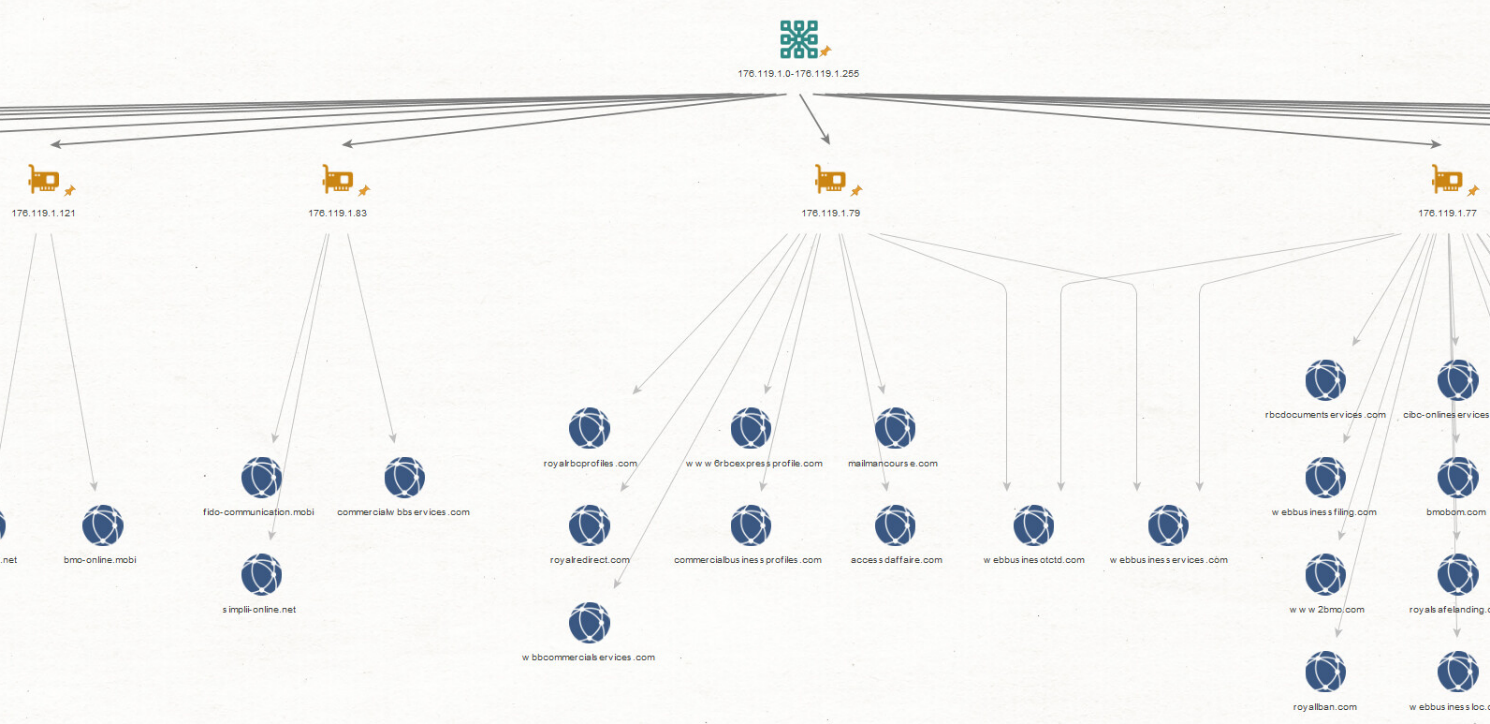
Figure 9: Phishing websites resolving to IPs on the same netblock


Figure 10: Examples of phishing pages from the same netblock
Blast from the Past
Some of the domains that we came across by looking up the related IP addresses had WHOIS records:

Figure 11: WHOIS information
Although the WHOIS records included fake information about nonexistent individuals, we were able to find other domains registered using the same details,
and we noticed an overlap with the infrastructure of a phishing attack targeting Canadian businesses reported back in 2017.

Figure 12: Old phishing infrastructure
Back then, the domains resolved to IP addresses on a different netblock under the same ASN: 176.119.5[.]0/24.

Figure 13: Shared WHOIS Information
Overall, we tracked more than 300 look-alike domains that hosted phishing websites for the following banks:
- The Royal Bank of Canada
- Scotiabank
- BMO Bank of Montreal
- Interac
- Tangerine
- Desjardins Bank
- CIBC Canadian Imperial Bank of Commerce
- TD Canada Trust
- Simplii Financial
- ATB Financial
- American Express
- Rogers Communications
- Coast Capital Savings
- Wells Fargo
Indicators of Compromise
IP Addresses
176.119.1[.]76
176.119.1[.]77
176.119.1[.]79
176.119.1[.]80
176.119.1[.]82
176.119.1[.]83
176.119.1[.]84
176.119.1[.]85
176.119.1[.]86
176.119.1[.]121
176.119.1[.]122
176.119.1[.]123
176.119.1[.]124
176.119.1[.]125
176.119.1[.]126
176.119.5[.]122
176.119.5[.]123
176.119.5[.]124
176.119.5[.]125
176.119.5[.]126
176.119.5[.]162
176.119.5[.]163
176.119.5[.]164
176.119.5[.]178
176.119.5[.]179
176.119.5[.]180
176.119.5[.]181
176.119.5[.]226
111.90.151[.]82
111.90.151[.]83
111.90.151[.]84
111.90.151[.]112
PDF SHA1
40df19cce707b99b9124ecedbdb37f72a913b9fb
7124d5e9e70a4c0f0c3a38f89cfdd3d105dbf7b9
c80e340770432fda95ab7e2483eb4d98df07b12d
4ad806857676df0e5572d5c5c987817cae400546
9d8d85b48c5b190ffb9d382c1edae4385c6d022a
f8979debd5e682f36c2cf036bb4837969abca0e9
92c1a6fb5b8d79d8de51715fe35608856863dd22
cb80764deff2ee2c7dc5afe041f36fdd21857a8d
c02cf08ad040b659603e8bb7d8d9787183757a79
b5dc6eb53f6c8b0a3880f84449943e3d1e36c272
569c05436c9d24dabb8de6d2354ab625d808f00b
27d8d13743b93507ca26faa5f71b533f3d8019b6
374b7e4d3268db0161b12fb38366b02954b486a6
ae01f57cef03489ae769ffba11e31ec71d585abb
7fe1207c8dddec9b0fc8a9c29d29194a02460d4c
a41e005c11dd9c98a7bdd4e200e044c8b1aa92de
b1be3bb8c7203bdcb89199d5f43dfff9296e62cc
ec51945aa4825c39f9fb39403a11dbf70e1a5a27
64797cd01d01256f356742b3b9df4c564cbb52c1
Check Point successfully intercepted these described attacks and was able to block all of the malicious attachments involved in this campaign.
Sandblast technologies –Threat Emulation and zero phishing, automatically recognized the malicious links within the phishing documents and successfully blocked this threat.





