

Introduction
Last weekend we issued a ransomware alert about a wave of attacks using a never-seen-before strain dubbed ‘Pay2Key.’ Our investigation suggested the ransomware operators were mostly targeting Israeli companies. The ransomware used in the attacks spread rapidly across victims’ networks, leaving significant parts of the network encrypted along with a ransom note, threatening to leak stolen corporate data unless the ransom is paid.
As more and more reports on Pay2Key attacks have accumulated, we started seeing victims paying the ransom because they were unwilling to take the risk of finding their sensitive corporate data being posted online. However, this unfortunate situation also created an opportunity to understand who is behind this new ransomware.
In this follow up article, we will share some of our new findings, along with how we traced the Bitcoin transactions from the attackers’ ransom notes, all the way to an Iranian based Bitcoin exchange. This was made possible by a joint effort with Whitestream – a blockchain intelligence firm.
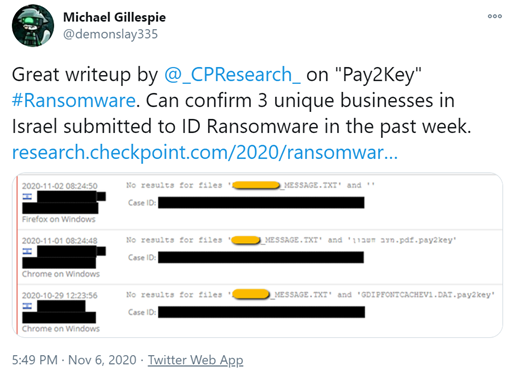
More Sightings
Shortly after we published the initial analysis, we received more information from various sources — shedding light on this new and mysterious campaign. Putting the information together revealed the special focus that the actors behind Pay2Key have given to Israeli companies, although a new report by Swascan, states that at least one victim has been targeted in Europe.
Double Extortion
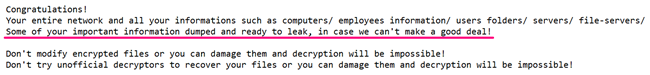
Double Extortion, a recent evolution in the ransomware arena we reported lately, is a tactic that applies extra pressure on victims to pay the ransom by threatening to leak corporate data stolen from the victims’ networks online.
As reported in our initial analysis, the Pay2Key operators follow this trend – threatening victims through the ransom note they left, to leak “important information.. in case we can’t make a good deal!”
It seems like the Pay2Key authors are willing to make good on their threats, as they have launched a new Onion website dedicated to sharing leaked data stolen from non-paying Pay2Key victims.
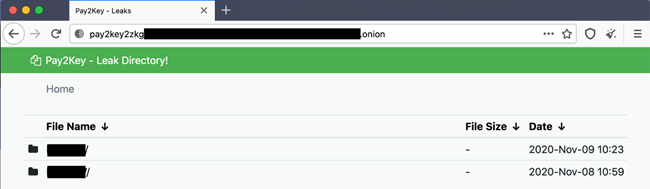
So far, the non-paying victims of this double extortion attack are three Israeli companies, and by the time this report is published there might be more of them. The leaked data of each victim company was uploaded to a dedicated folder on the website, accompanied with a tailored message from the attackers. In the massage they share sensitive information regarding the digital assets of the victim, including details regarding their domain, servers and backups.
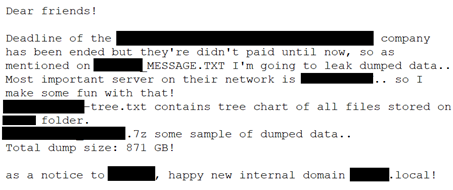
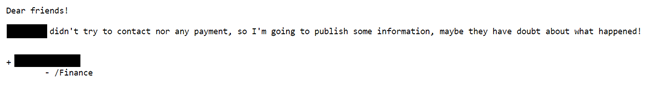
To better understand the extortion method, we are sharing the tactics the hacker used in this Double Extortion campaign – one against a gaming development company and the other against a law firm.
While in the case of the law firm a lot of sensitive information was immediately leaked upon deadline, in the case of the game development company, the attackers offered a second chance to make payment, and started with posting only a detailed file system tree scheme of the victim’s NAS servers. A day after however, they have already leaked a “Finance” related folder, urging the victim to pay before any additional information is leaked. In both cases the attackers mentioned they had hundreds of Gigabytes of stolen data.
Following the Money
While the aforementioned victims decided not to pay the ransom, there were at least four victims who chose to pay. These unfortunate circumstances created an opportunity to follow the money and to get a sense of who might be behind the Pay2Key targeted ransomware attack.
Along with Whitestream, we followed the sequence of transactions, which began with the deposit of the ransom and ended at what appeared to be an Iranian cryptocurrency exchange named Excoino.
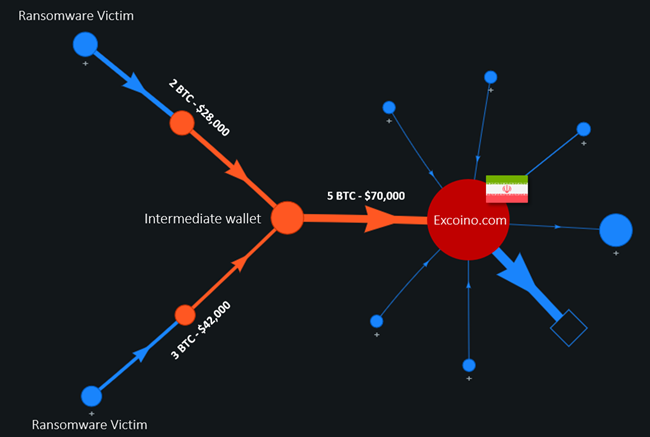
The flow starts with Bitcoin wallets found in the ransom notes. Once the victim deposits to the ransom wallet specified in the ransom note, the attackers proceed with transferring the money to an intermediate wallet – this wallet was seen to be reused in ransom payments of several victims. Then the Bitcoin is transferred to a final wallet address associated with a high activity cluster. These types of high activity clusters often suggest an association with a financial entity involved with the Bitcoin market, often an exchange.
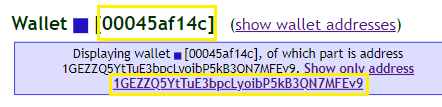
In order to verify the link between this “final wallet” and the Excoino exchange, we used the WalletExplorer service and a known Excoino wallet address.
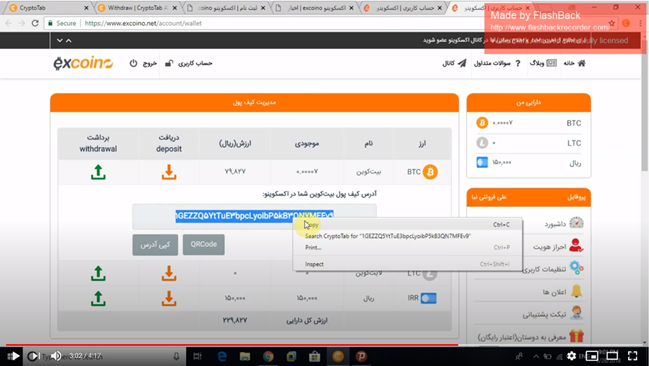
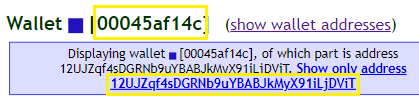
Analyzing the bitcoin address found in Figure 7, as well as our “final wallet” , we can see they both share the same cluster id [00045af14c] according to WalletExplorer.
Excoino is an Iranian company that provides secure cryptocurrency transactions services for Iranian citizens. Registration requires the user to have a valid Iranian phone number and ID/Melli code (کد ملی). To be eligible to trade the exchange, however, will also require a copy of the ID itself.
In it’s terms and conditions, Excoino states the first transaction (and any other suspicious transaction) will have to be reported to the Iranian Cyber Police, FATA, for further investigation.
This may suggest the owners of the final wallets are Iranian citizens, who most probably are behind the Pay2Key attack on Israeli companies last week.
Conclusion
The Pay2Key operators have proceeded to the double extortion stage of their attack, leaking data of some of their “customers”, trying to force them (and others) to pay.
In order to track the activities of the threat actor behind Pay2Key, we decided to focus on the cryptocurrency wallets found in the ransom notes, tracing the money flow to an Iranian based exchange.
This, together with the fact that the attacks seem to be focused on Israeli entities, strengthens our assumption that this wave of attacks is indeed executed by an Iranian based threat actor.
Pay2Key is only the last wave in a series of Iranian based targeted ransomware attacks deployed against Israeli organizations throughout recent months, in what appears to be a growing trend.
Prevention Recommendations
- Intrusion Prevention Systems (IPS) – detect or prevent attempts to exploit weaknesses in vulnerable systems or applications, protecting you in the race to exploit the latest breaking threat. Check Point IPS protections in our Next Generation Firewall are updated automatically.
- Anti-Ransomware – an Anti-Ransomware solution defends organizations against the most sophisticated ransomware attacks, and safely recovers encrypted data, ensuring business continuity and productivity.
- SandBlast Agent – A complete endpoint security solution identifies ransomware behaviors such as file-encryption or attempts to compromise operating system backups, and safely restores ransomware-encrypted files automatically





