

Research by :Oded Vaanunu / Roman Zaikin / Dan Lasker
Chess.com is the world leading platform for online chess games. It is an internet chess server, news website, and social networking website. Chess.com has a strong focus on community-based forums and blogs. These social features allow players to connect with each other, become friends, share their thoughts and experiences, and learn from each other.
There are over 93 million members from all around the world and over 2.5 million active members daily.
One of the largest chess platforms in the world, Chess.com has hosted online tournaments such as the “Chess.com Global Championship,” in which the winner wins $1,000,000.
What happened in 2022?
In 2022, Magnus Carlsen (Norwegian World champion since 2013) decided to withdraw from a tournament because he believed that Hans Niemann (American Grand Master) was a cheater.
Chess.com claimed : “Niemann has likely cheated in more than 100 Online Chess Games […] he is the fastest rising top player in classical OTB chess in modern history”.
Chess.com decided to remove Niemann from the platform and from the Global Chess Championship the day after he beat GM Magnus Carlsen. This decision has been made because Hans admitted that he cheated in chess games on the popular website in 2020. Chess.com used its cheating-detection software and discovered suspicious play.
Websites for reference:
https://www.nytimes.com/2022/12/04/business/chess-cheating-scandal-magnus-carlsen-hans-niemann.html
https://www.bbc.com/news/world-63010107
Chess.com invests a lot of money in trying to detect cheaters that use various kinds of technique. Cheating in chess is a deliberate violation of the rules of chess or other behavior that is intended to give an unfair advantage to a player or team. It can occur in many forms and can take place before, during, or after a game.
Chess.com [AP1] participation relates to the rating of players to participate in games and win bigger prizes. For example, tournaments are based on ratings.
We decided to test the popular online platform Chess.com to try to check if it is possible to cheat in the games by abusing a security vulnerability.
- We found out that it is possible to win by decreasing the opponent’s time and winning the game over time, without the opponent noticing what happened.
- In addition, it is possible to extract successful chess moves to solve online puzzle challenges and win puzzle ratings. In this method, we simply need to catch the communication between the client side (player) and the server (Chess.com website). The server accidentally sends the correct solution to the puzzle! We can then abuse and cheat on puzzle championships (in which the winner gets prize money) by simply submitting the correct moves that we found. Moreover, it is possible to modify the elapsed time it took to think about the solution.
Technical Details:
Chess.com uses WebSocket for inner-game communication and various tasks; each game contains a game id which can be seen in the URL:

If the game is played by friends, Chess.com provides an additional feature to the gameplay, that allows to “Add 15 Seconds” to the opponent:
Pressing on the button will add 15 seconds to the opponent, and the request looks like that:
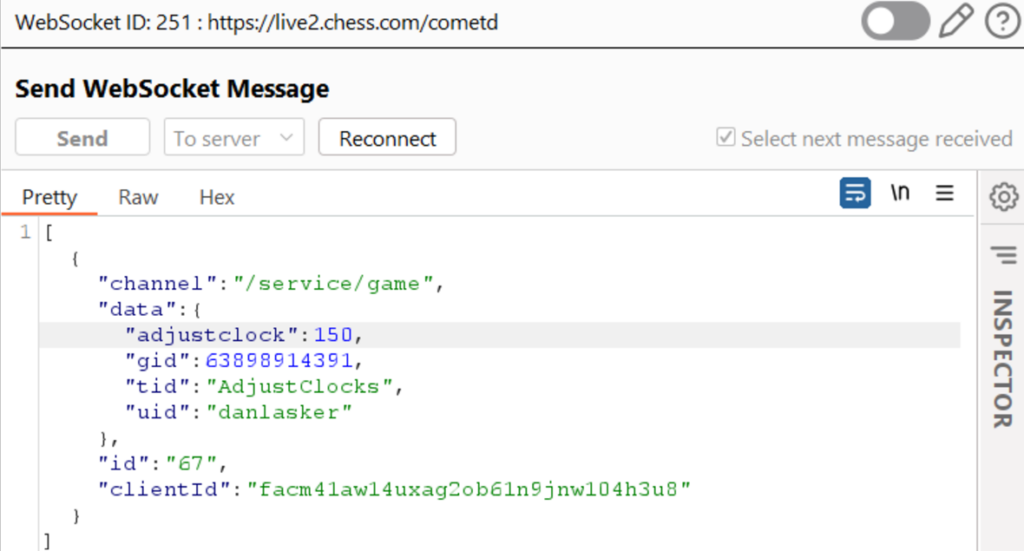
Let’s dive into the parameters that are sent to the server:
- channel – path to the game itself.
- data – contains 4 attributes:
- adjustclock – how much time we want to add to the opponent (150 = 15 seconds)
- gid – Identifier of the current game.
- tid – current task to perform, in this case it is adjustclocks in order to add time to the opponent.
- uid – Identifier of the opponent.
- id – socket sequence number which is auto-incremented every time a WebSocket request is sent.
- clientId – user click id (in this example, this is the attacker id).
We have found that it is possible to win any game if the attacker sends a friend request during/before the game to the opponent, and the opponent approves it.
We can think of a scenario in which the attacker-friendly chats with its opponent during the game. The innocent opponent (victim) approves the friend request without a doubt. Finally, the option of “adding time” is provided, and the attacker abuses it in order to reduce the timing clock of the victim to 0.
The attacker is ab
le to intercept the WebSocket request with any proxy tool (e.g. BurpSuite) and to change the sending request to https://live2.chess.com/cometd with the following adjustclock data:
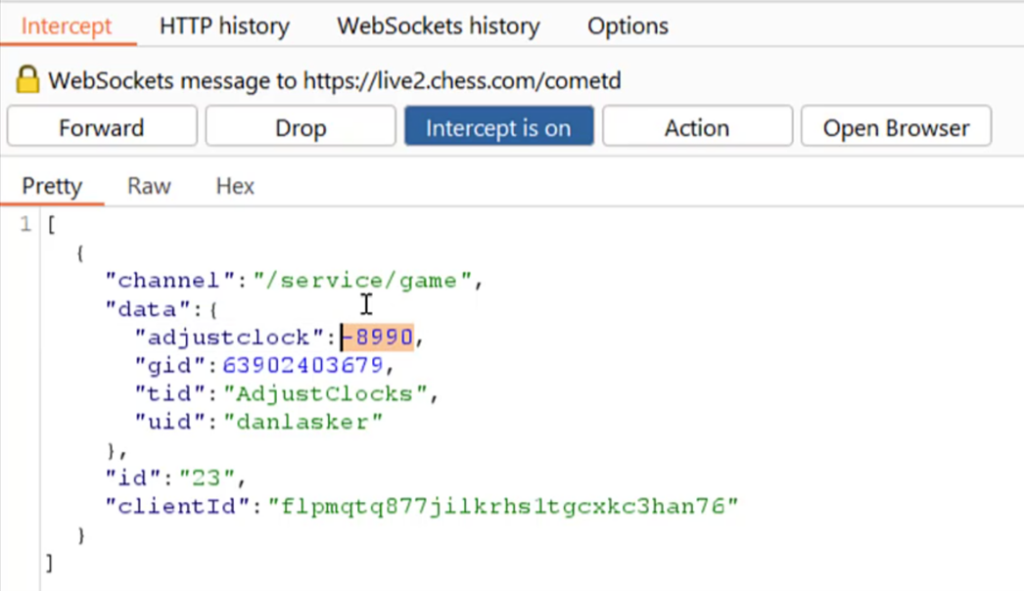
In this request the sending adjustclock value is -8990 and as a result the opponent will have just 10 seconds to play and will certainly lose the game without noticing that its time on the clock has been considerably reduced:
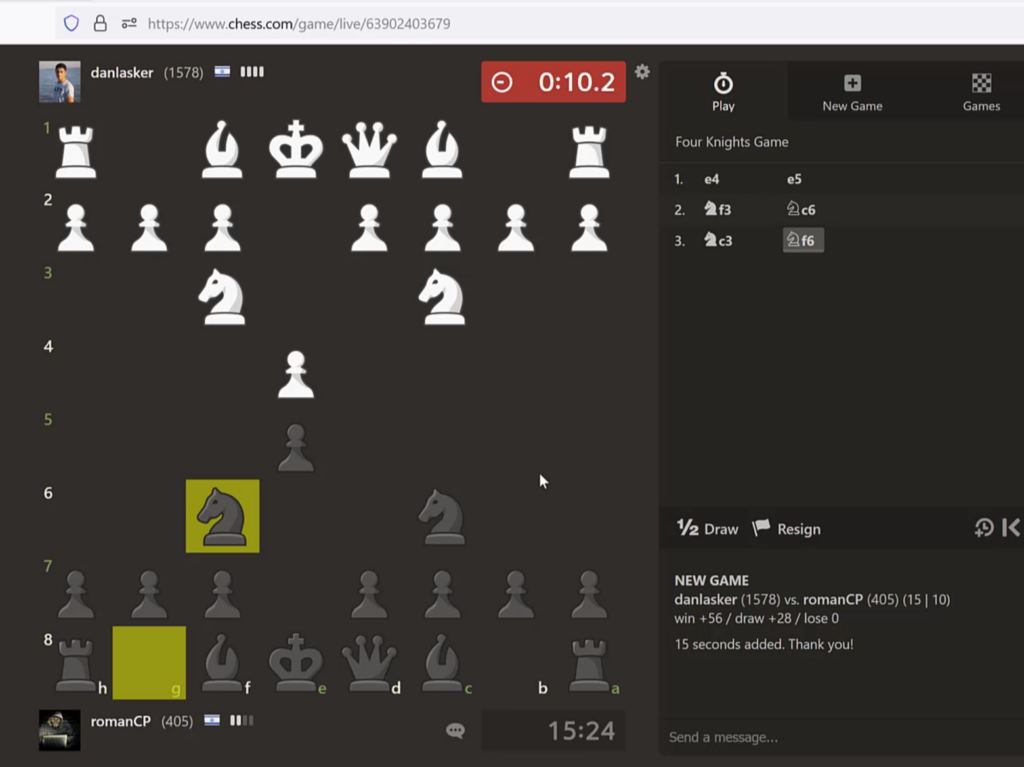
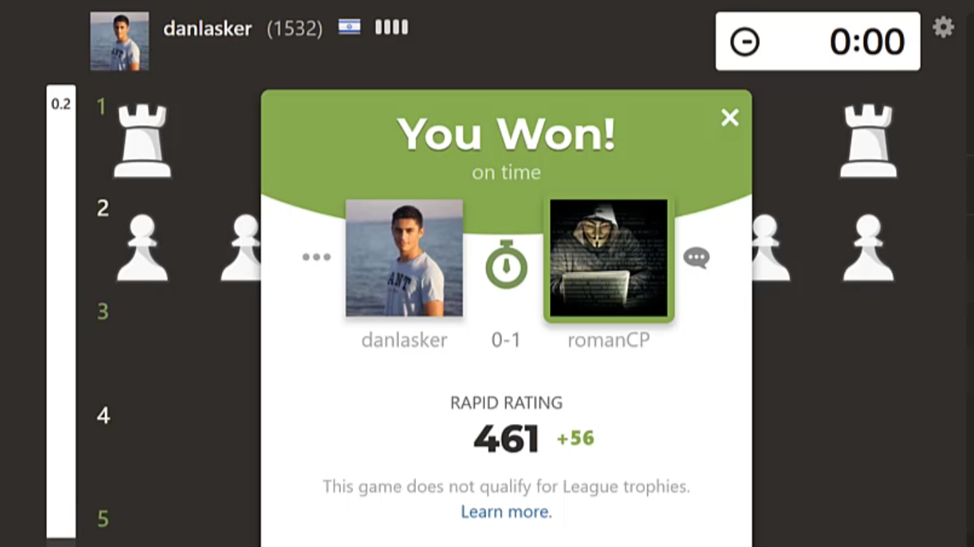
In conclusion, it is possible to win any game if the opponent approves the friend request:
Because rating is very important in chess and the integrity of the game and the puzzles the player solves, we also looked at the puzzle’s logic and found out that it is also possible to solve the puzzle with only one modified request.
Explanation of the puzzle’s logic based on two requests:
First is an HTTP request https://www.chess.com/callback/tactics/rated/next which contains the following important parameters:
- id – the challenge identifier to be submitted
- tcnMoveList – the challenge solution, the expected solution to be sent to the server
- averageSeconds – the average solve rate
Here is an example of this request.
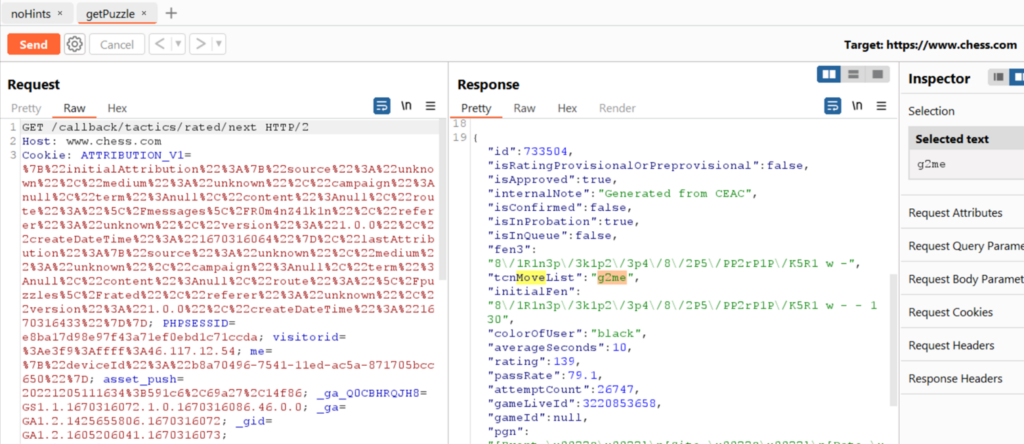
The MoveList is the actual solution for the puzzle and is expected by the server in order to confirm that the challenge is correctly solved.
All the attacker needs to do in order to solve the puzzle is to send that list of movers to the request to https://www.chess.com/callback/tactics/submitMoves with the 3 modified parameters:
- tacticsProblemId – identifier of the challenge.
- totalTime – time that took us to solve the challenge, which can be the average time from the previous request.
- moves – the value of tcnMoveList, which is the actual solution to the puzzle.
By sending those parameters without even playing allows the attacker to raise his score:
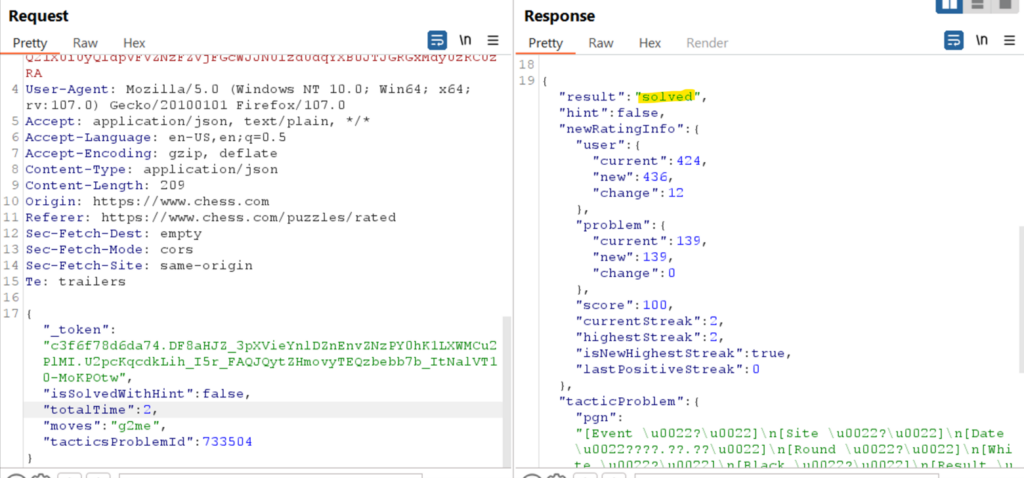
This is how it is possible to cheat in puzzles and to win ranking without playing:

Responsible disclosure:
CPR has disclosed this information to the chess.com teams which acknowledged the vulnerability and applied a fix
to it.





