Check Point Research and the cyber intelligence company, CyberInt, have collaborated to discover the next generation in phishing kits, currently being advertised on the Dark Net. Unlike previous kits which are primarily composed of just one or two pages to collect personal or financial data, this new and advanced phishing kit offers much more in order to create a more convincing fake site.![]()
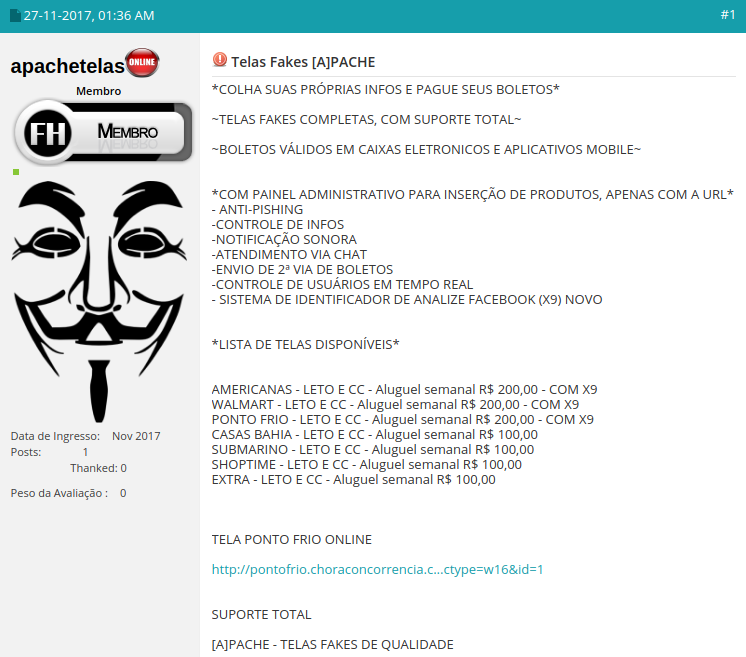
Created by a character called ‘[A]pache’, it offers those with low technical know-how to manage their own phishing campaigns to collect the personal and financial information of unsuspecting consumers.
Below we will show how [A]pache’s phishing kit works and how it is used to carry out online scamming operations.
The Advertisement
[A]pache makes it very easy for those with very little technical ability to get carry out their own cyber-attack. By simply downloading his multi-functioning phishing kit and following his installation instructions, it would not take long before a threat actor is able to launch his campaign.
Figure 1: Posting that advertises the [A]pache phishing kit.
At $100-$300, the cost is higher than more standard phishing kits. Standard kits usually retail at $20-$50, with some even free, as they only provide login pages and prompts for personal and financial information. With [A]pache’s phishing kit however, threat actors are provided with a full suite of tools to pull carry out their attack. These include a whole backend interface with which they can create convincing fake retail product pages and manage their entire campaign.
The Retail Targets
[A]pache’s phishing kit offers many well-known brands to choose from. Options include: Walmart, Americanas, Ponto Frio, Casas Bahia, Submarino, Shoptime and Extra. As most of these retailers are for a Brazilian audience, it seems this kit is aimed at those with a good knowledge of Portuguese, though we also found some kits that targeted US brands too.
The Kit’s Configuration Panel
In order to convincingly persuade their victims that they are shopping at the genuine site they think they are at, online scammers then need a domain that is similar to the targeted brand, for example, www.walmart-shopping.com. Once registered, they are ready to deploy the kit to a PHP and MySQL supported web host. They can then log in to the kit’s admin panel and begin configuring their campaign.
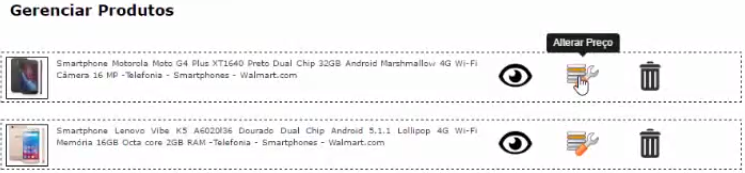
Figure 2: The kit’s admin panel.
Configuration options include:
- Email: Select the email address for notifications of new phished information to be sent to.
- URL: Select the URL upon which the phishing site sits.
- Payments: Choose to disable ‘Boleto Bancário’. This will force the potential victims to enter their credit card data, or display fake Boleto details.
- Product Management: Insert legitimate product URLs from the target retailer’s website for automatic import and configure the display price to lure targets.
- Victim Information Management: Once the victims have been ‘phished’, their information can be displayed within the admin panel, both in full and as a list of credit card details.
Adding Products to Fake Site
To simplify this process, [A]pache has made a simple user interface within the admin panel where the threat actor can paste the product URL of the legitimate retailer and the kit will automatically import the product information into the phishing page. They can then view their ‘products’ and change their original prices.
Figure 3: Product price setting in the admin panel.
Setting Product Prices
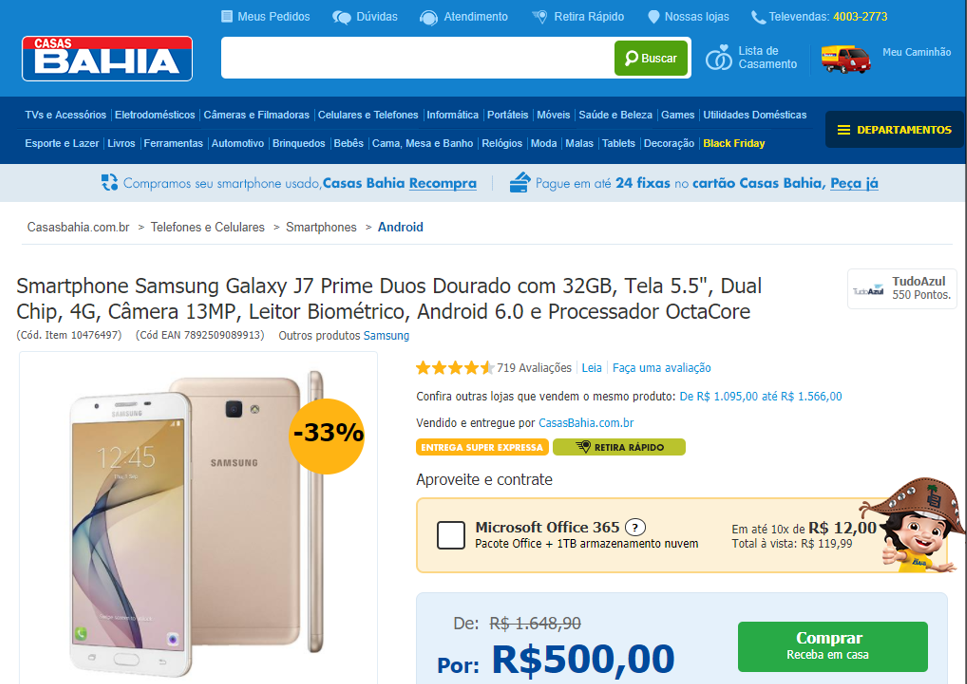
Like any shop, the fake phishing site encourages it users to also be competitive, so it is suggested that the product prices be attractive. This would help motivate potential ‘customers’ to click on the items and proceed to checkout. Reducing prices too low though would raise suspicions with captivated ‘customers’.
In addition, one trick is to list highly valued and desired items first, like smartphones, to entice potential victims.
The threat actor is now set to promote their site and bring in his unsuspecting victims.
Figure 4: Product price setting in the admin panel.
Heading to Checkout
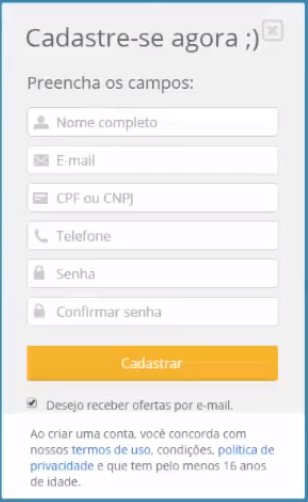
When customers click through from the threat actor’s email, social media link or any other way in which they could be sending traffic, the site will look exactly like the target site and customers can proceed to checkout with no suspicions raised. At this point they would enter their payment and delivery details.
Figure 5: Payment form as served by the phishing kit.
[A]pache’s high-end phishing kit also comes with an automated post-code look-up function for added conviction.
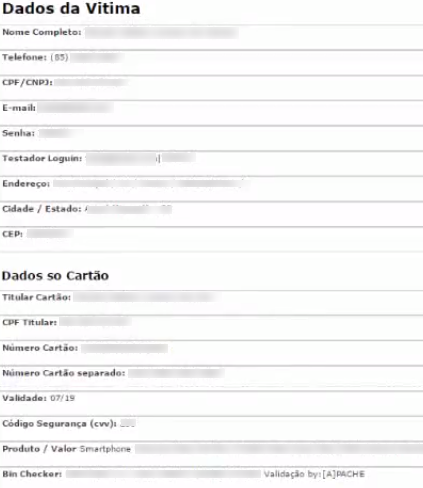
Collecting Credit Card Details
With payment details entered and sent straight to the threat actor’s database, including the CVV, the cyber criminal can then check the kit’s back-office admin panel to see the victim’s personal and financial information.
Figure 6: Admin panel collects victim’s information.
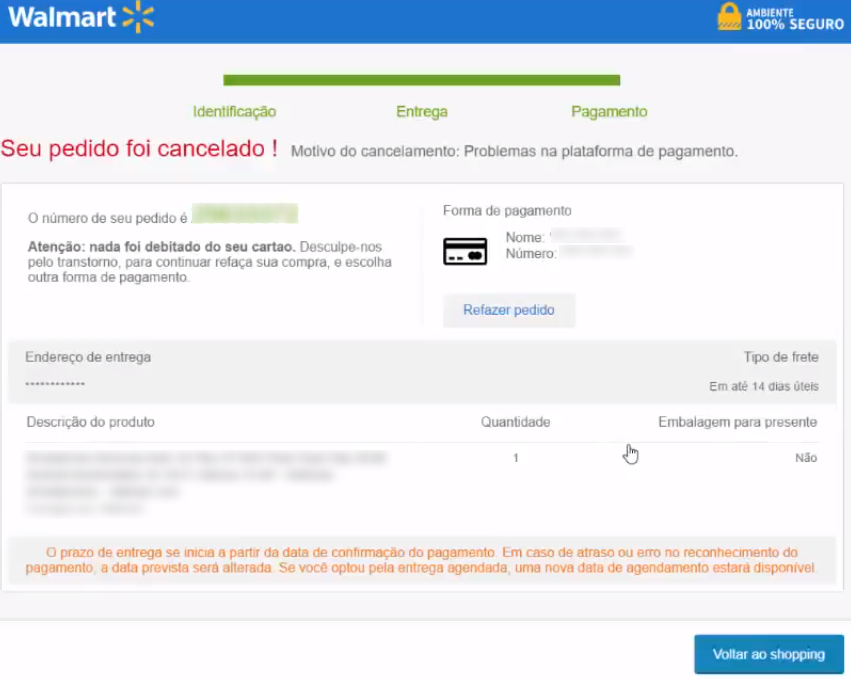
Meanwhile, after the victim has entered their payment details, they are presented with a notification that the payment process has failed. This helps convince them to not be concerned when the purchased fake product does not arrive.
Figure 7: Payment error page shown to victim.
Who Is [A]pache?
Our research team was able to track down the perpetrator behind this Brazilian phishing kit, and who may well also be behind others kits targeting US victims.
Once an attack is over, cyber criminals often take down the fake retail site in order to lower the risks of being caught. In this case however, we found a custom built ‘error 404’ site in use.
Figure 8: The error 404 page found in the phishing kit.
This unique landing page was created by a web designer who is likely unaware that ihs work is being used for malicious purposes. While we did not notice any legitimate websites using this 404 page, and discovered that ‘Blue World Electronicos’ does not exist, we did notice an English version of this page being used online. In fact, we found a few domains, serving PayPal phishing scams, using the English version of this page.
From this landing page we managed to find the actual phishing kit along with its admin panel. This led us to the next clue in discovering [A]pache’s identity.
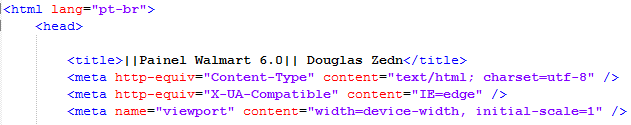
Looking into the code of the kit, we discovered that [A]pache had included his handle, ‘Douglas Zedn’, in the control panel of the Walmart phishing site. This was either a mistake or he was looking for some kind of recognition for his work.
Figure 9: The phishing kit’s source code revealing [A]pache’s handle.
‘Douglas’ had also included a profile image in the resource kit too.
Figure 10: [A]pache’s avatar as seen in his phishing kit’s resources.
When carrying out a basic online search, as seen on his Steam social media profile page, we then discovered that ‘Douglas’ uses the same identity for his business life as he does for his personal life.
Figure 11: [A]pache’s Steam social media profile.
With one more step we were able to trace ‘Douglas Zedn’ back to his Twitter handle to find the real person behind the avatars.
Figure 12: The real [A]pache.
With some reports claiming that 91% of cyberattacks and data breaches begin with a phishing email, phishing remains a constant threat for stealing financial information, intellectual property, and even interfering with elections. For this reason, consumers and businesses alike must ensure they have the latest protections for safe guarding against such threats.
—————————————————————————————————————————————————–
About CyberInt:
In the age of digital transformation businesses are opening themselves up to far greater risks and greater threats in their environment. CIOs and CISOs are therefore beginning to look at their security environment through a digital lens. CyberInt has been recognized by both Gartner and Forrester as an innovator in securing digital businesses.
CyberInt’s Managed Detection and Response services span globally and include some of the top finance, retail and telecommunication organizations. MDR services allow our customers to combat and respond to advanced cyber threats that would normally go unnoticed by standard security controls, while protecting their brand, digital assets and customers.
For further information, please visit www.cyberint.com.