

Looking back at the first half of 2017, the word ransomware is probably one of the first that come to mind, courtesy of WannaCry and the more recent Petya attacks that dominated the news headlines. Indeed, according to our data, more than 50% of cyber-attacks in the Americas, Europe and the Middle East were ransomware, making it the prevalent attack type in these regions. Furthermore, the percentage of ransomware attacks out of the main categories in all three regions almost doubled in the first half of 2017 compared to the first half of 2016 – from an average of 26% to an average of 48% of the three main attack categories worldwide. The second word that comes to mind might be one three letter agency (or the other), courtesy of which were the vulnerabilities exploited by these attacks. And indeed, perhaps the most worrisome new trend is “nation-state level malware” for the masses – as these leaked sophisticated capabilities can now haunt virtually everyone, rather than the selected strategic targets they were initially designed for. However even these types of sophisticated attacks could have been prevented, had enterprises utilized solutions that are available on the shelf today, such as network micro-segmentation, threat emulation and extraction and endpoint security.
The other type of malware that haunts all of us may seem less threatening at first, but a deeper look shows otherwise: fraudulent advertising malwares are largely backdoors that may enable full, privileged, control of the victim’s device, be it a pc or mobile. It’s only a matter of time until the monetization vector of this type of attacks changes to cause tangible damage, as the attack surface is vast already. Fireball and Hiddad top the malware “hit charts” for 2017 so far (in pc and mobile respectively), both capable of obtaining sensitive data from the infected devices. From the adware perspective, 2017 has definitely been the year of the rooster so far, as the prominent adware this year – such as Fireball, Hummingbad and others – originate from China.
Interestingly, in APAC countries one has the same chances to get infected by mobile, ransomware or banking malware, as they have the same “market share”, each with about one third of the victims. However, the number of mobile attacks in this region has significantly grown this year: 32% in these last 6 months as opposed to 22% in the end of 2016. The rise of mobile attacks infected an alarming number of devices with malicious code, enabling attackers to steal information and engage in fraudulent activities.
The sophistication of the 2017 attackers does not stop at variating the vectors and surfaces, but also in the payload itself and its delivery method. Our investigation revealed a brand new method of attack exploitation where a mouse hover over a malicious hyper-link in a Power Point presentation (without actually clicking on it) is already enough to get infected.
Mobile malware developers have not stayed behind, as injecting code to Android system processes has become almost a standard for Android cybercriminal groups and threat actors. Both Triada – the third most common mobile malware in the world and CopyCat – the most recent discovery of Check Point mobile researchers, inject code into Zygote – a daemon responsible for launching apps in the Android operating system. This allows the malwares to control any activity on the device and enables a one-stop attack that facilitates fraud, information stealing and disruption of all relevant apps – financial, social, productivity, etc.
The evolving sophisticated techniques we identified may utilize the mobile device as an entry point to the enterprise network, providing access to proprietary information, software and other assets. Unfortunately even though it’s already 2017, only a relatively small percentage of enterprises use the mobile threat prevention security products available on the market today. The trend of sophisticated mobile attacks can only be diminished when mobile solutions become common practice for business organizations.
Top Malware Families (Global)
The numbers in the below graph represent the percentage of organizations that were affected by the malware.
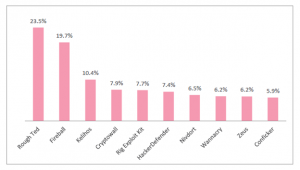 Figure 1: Most Prevalent Malware Globally
Figure 1: Most Prevalent Malware Globally
Cyber Attack Categories by Region
The infographic below shows the spread by region of three of the main malware categories: banking, mobile and ransomware.
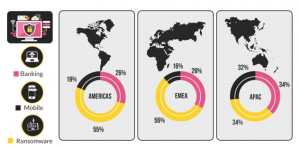 Figure 2: Attack Categories by Region
Figure 2: Attack Categories by Region
Knowledge is power, and it also lies in the foundation of orchestrating the organization’s infrastructure to deal with the prevention of these threats on all levels: network, endpoint and mobile. The Check Point H1 2017 Global Threat Intelligence Trends report and the Check Point H1 2017 Regional Threat Intelligence report provide you with a comprehensive overview of the malware landscape in the top categories of ransomware, banking and mobile threats, based on threat intelligence data drawn from the ThreatCloud World Cyber Threat Map between January and June of 2017.
For more information:





